Articles

Inside the Axios supply chain compromise - one RAT to rule them all
Elastic Security Labs analyzes a supply chain compromise of the axios npm package delivering a unified cross-platform RAT

Elastic releases detections for the Axios supply chain compromise
Hunting and detection rules for the Elastic-discovered Axios supply chain compromise.

TOLLBOOTH: What's yours, IIS mine
REF3927 abuses publicly disclosed ASP.NET machine keys to compromise IIS servers and deploy TOLLBOOTH SEO cloaking modules globally.

TOLLBOOTH: What's yours, IIS mine
REF3927 abuses publicly disclosed ASP.NET machine keys to compromise IIS servers and deploy TOLLBOOTH SEO cloaking modules globally.

MCP Tools: Attack Vectors and Defense Recommendations for Autonomous Agents
This research examines how Model Context Protocol (MCP) tools expand the attack surface for autonomous agents, detailing exploit vectors such as tool poisoning, orchestration injection, and rug-pull redefinitions alongside practical defense strategies.

From South America to Southeast Asia: The Fragile Web of REF7707
REF7707 targeted a South American foreign ministry using novel malware families. Inconsistent evasion tactics and operational security missteps exposed additional adversary-owned infrastructure.

Invisible miners: unveiling GHOSTENGINE’s crypto mining operations
Elastic Security Labs has identified REF4578, an intrusion set incorporating several malicious modules and leveraging vulnerable drivers to disable known security solutions (EDRs) for crypto mining.
STIXy Situations: ECSaping your threat data
Structured threat data is commonly formatted using STIX. To help get this data into Elasticsearch, we’re releasing a Python script that converts STIX to an ECS format to be ingested into your stack.

Unmasking a Financial Services Intrusion: REF0657
Elastic Security Labs details an intrusion leveraging open-source tooling and different post-exploitation techniques targeting the financial services industry in South Asia.
Elastic catches DPRK passing out KANDYKORN
Elastic Security Labs exposes an attempt by the DPRK to infect blockchain engineers with novel macOS malware.

Introducing the REF5961 intrusion set
The REF5961 intrusion set discloses three new malware families targeting ASEAN members. The threat actor leveraging this intrusion set continues to develop and mature their capabilities.
The DPRK strikes using a new variant of RUSTBUCKET
Watch out! We’ve recently discovered a variant of RUSTBUCKET. Read this article to understand the new capabilities we’ve observed, as well as how to identify it in your own network.
Initial research exposing JOKERSPY
Explore JOKERSPY, a recently discovered campaign that targets financial institutions with Python backdoors. This article covers reconnaissance, attack patterns, and methods of identifying JOKERSPY in your network.

PHOREAL Malware Targets the Southeast Asian Financial Sector
Elastic Security discovered PHOREAL malware, which is targeting Southeast Asia financial organizations, particularly those in the Vietnamese financial sector.
Ingesting threat data with the Threat Intel Filebeat module
Tutorial that walks through setting up Filebeat to push threat intelligence feeds into your Elastic Stack.

The Elastic Container Project for Security Research
The Elastic Container Project provides a single shell script that will allow you to stand up and manage an entire Elastic Stack using Docker. This open source project enables rapid deployment for testing use cases.

Update to the REF2924 intrusion set and related campaigns
Elastic Security Labs is providing an update to the REF2924 research published in December of 2022. This update includes malware analysis of the implants, additional findings, and associations with other intrusions.

SiestaGraph: New implant uncovered in ASEAN member foreign ministry
Elastic Security Labs is tracking likely multiple on-net threat actors leveraging Exchange exploits, web shells, and the newly discovered SiestaGraph implant to achieve and maintain access, escalate privilege, and exfiltrate targeted data.

Exploring the REF2731 Intrusion Set
The Elastic Security Labs team has been tracking REF2731, an 5-stage intrusion set involving the PARALLAX loader and the NETWIRE RAT.

Operation Bleeding Bear
Elastic Security verifies new destructive malware targeting Ukraine: Operation Bleeding Bear

KNOTWEED Assessment Summary
KNOTWEED deploys the Subzero spyware through the use of 0-day exploits for Adobe Reader and the Windows operating system. Once initial access is gained, it uses different sections of Subzero to maintain persistence and perform actions on the host.

Detection rules for SIGRed vulnerability
The SIGRed vulnerability impacts all systems leveraging the Windows DNS server service (Windows 2003+). To defend your environment, we recommend implementing the detection logic included in this blog post using technology like Elastic Security.

Doing time with the YIPPHB dropper
Elastic Security Labs outlines the steps collect and analyze the various stages of the REF4526 intrusion set. This intrusion set uses a creative approach of Unicode icons in Powershell scripts to install a loader, a dropper, and RAT implants.

ICEDIDs network infrastructure is alive and well
Elastic Security Labs details the use of open source data collection and the Elastic Stack to analyze the ICEDID botnet C2 infrastructure.
Detecting and responding to Dirty Pipe with Elastic
Elastic Security is releasing detection logic for the Dirty Pipe exploit.

Elastic protects against data wiper malware targeting Ukraine: HERMETICWIPER
Analysis of the HERMETICWIPER malware targeting Ukranian organizations.
Extracting Cobalt Strike Beacon Configurations
Part 2 - Extracting configurations from Cobalt Strike implant beacons.

CUBA Ransomware Campaign Analysis
Elastic Security observed a ransomware and extortion campaign leveraging a combination of offensive security tools, LOLBAS, and exploits to deliver the CUBA ransomware malware.

LUNA Ransomware Attack Pattern Analysis
In this research publication, we'll explore the LUNA attack pattern — a cross-platform ransomware variant.

Exploring the QBOT Attack Pattern
In this research publication, we'll explore our analysis of the QBOT attack pattern — a full-featured and prolific malware family.

Playing defense against Gamaredon Group
Learn about the recent campaign of a Russia-based threat group known as Gamaredon Group. This post will review these details and provide detection strategies.

Going Coast to Coast - Climbing the Pyramid with the Deimos Implant
The Deimos implant was first reported in 2020 and has been in active development; employing advanced analysis countermeasures to frustrate analysis. This post details the campaign TTPs through the malware indicators.

FORMBOOK Adopts CAB-less Approach
Campaign research and analysis of an observed FORMBOOK intrusion attempt.
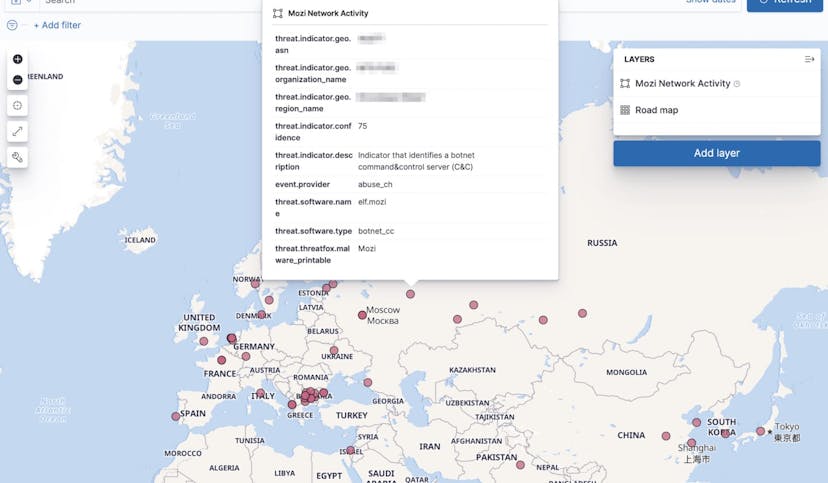
Collecting and operationalizing threat data from the Mozi botnet
The Mozi botnet is an ongoing malware campaign targeting unsecured and vulnerable networking devices. This post will showcase the analyst journey of collecting, analyzing, and operationalizing threat data from the Mozi botnet.

Detection and response for the actively exploited ProxyShell vulnerabilities
In the last week, Elastic Security has observed the exploitation of Microsoft Exchange vulnerabilities associated with ProxyShell. Review the post to find newly released details about this activity.
Collecting Cobalt Strike Beacons with the Elastic Stack
Part 1 - Processes and technology needed to extract Cobalt Strike implant beacons
