Citrix Web App Firewall Integration for Elastic
| Version | 1.20.0 (View all) |
| Subscription level What's this? |
Basic |
| Developed by What's this? |
Elastic |
| Ingestion method(s) | File, Network Protocol |
| Minimum Kibana version(s) | 9.0.0 8.11.0 |
This AI-assisted guide was validated by our engineers. You may need to adjust the steps to match your environment.
The Citrix Web App Firewall integration for Elastic enables you to collect and analyze logs from Citrix ADC and NetScaler appliances. This integration provides visibility into your web application security posture by capturing detailed event data, including security violations, signature matches, and network metadata.
This integration has been tested and verified with the following third-party vendor versions:
- Citrix ADC version 13.1
- NetScaler version 10.0
The integration is designed to work with any Citrix or NetScaler appliance capable of exporting logs in the Common Event Format (CEF).
This integration collects logs from Citrix appliances by receiving syslog data over the network using TCP or UDP, or by reading logs directly from local files on the system. You'll deploy an Elastic Agent on a host configured as a syslog receiver or one that has access to the appliance's log files. The agent processes the incoming data—using the citrix_waf.log data stream—and forwards it to the Elastic Stack. For the best parsing results and data fidelity, it's recommended to configure your Citrix appliance to export logs in Common Event Format (CEF).
The Citrix Web App Firewall integration collects log messages of the following types:
- Citrix WAF logs (using Syslog): Citrix WAF logs transmitted over the network using TCP or UDP, including real-time security violations and signature match events.
- Citrix WAF logs (using File): Citrix WAF logs collected from local files on the system where the Elastic Agent is running.
- Application firewall logs: Detailed records of security violations, blocked requests, and signature matches generated by the WAF engine.
- Security event metadata: Information regarding the specific security check triggered, the action taken (such as block or log), and the severity of the event.
- Network metadata: Source and destination IP addresses, ports, and transport protocols involved in the web transactions.
The integration includes the following data stream:
log: This data stream captures security and audit logs including violations, signature matches, and system events.
You can use the Citrix Web App Firewall integration to support various security and operational requirements:
- Threat detection and response: Identify and mitigate web-based attacks such as SQL injection, cross-site scripting (XSS), and other security violations.
- Security posture assessment: Analyze signature matches and security event metadata to evaluate the effectiveness of WAF policies and identify areas for improvement.
- Compliance and auditing: Store security logs to meet regulatory requirements and provide a verifiable trail of security-related events for audits.
- Traffic analysis: Gain insights into network metadata, including source and destination patterns, to understand application usage and identify potential anomalies.
Before you can collect logs from Citrix Web App Firewall, ensure you meet the following requirements.
You need these Citrix-specific prerequisites:
- Administrative access with full credentials for the Citrix ADC / NetScaler management GUI or CLI.
- An active license for the Citrix Web App Firewall feature installed on your appliance.
- Unrestricted network access between the Citrix appliance and the Elastic Agent on the configured Syslog port, which defaults to
9001for this integration. - The ability to create and bind global audit policies to the
APPFW_GLOBALbind point. - A firmware version that supports Common Event Format (CEF) logging.
You need these Elastic prerequisites:
- Elastic Stack version 8.11.0 or later.
- An Elastic Agent installed on a host reachable by the Citrix appliance and enrolled in a Fleet policy.
- The Citrix WAF integration added to the Elastic Agent's policy using Kibana.
- Firewall rules that allow inbound traffic to the Elastic Agent on the specified Syslog port from the Citrix appliance's NSIP or SNIP.
Elastic Agent must be installed on a host that can receive syslog data or access the log files from your Citrix appliance. For more details, check the Elastic Agent installation instructions. You can install only one Elastic Agent per host.
Elastic Agent is required to stream data from the syslog or log file receiver and ship the data to Elastic, where the events will then be processed using the integration's ingest pipelines.
You must configure your Citrix NetScaler or ADC appliance to generate logs in Common Event Format (CEF) and send them to the Elastic Agent.
The integration requires logs in CEF for proper field mapping.
- Log in to the NetScaler or Citrix ADC management interface.
- Navigate to Security > Citrix Web App Firewall > Change Engine Settings.
- In the General Settings section, locate the CEF Logging checkbox.
- Check Enable CEF Logging.
- (Optional) Check GeoLocation Logging if you wish to include geolocation data in the logs.
- Click OK to save.
Alternatively, you can use the command line interface (CLI):
set appfw settings CEFLogging on
Define where the logs should be sent by specifying the Elastic Agent IP address and port.
- Navigate to Configuration > System > Auditing > Syslog.
- Click on the Servers tab and click Add.
- Configure the following details:
- Name:
Elastic_Syslog_Server - IP Address: Enter the IP address of your Elastic Agent (replace with your actual value).
- Port:
9001(or your configured port). - Transport Type: Select UDP or TCP.
- Log Level: Select ALL.
- Name:
- Click Create.
Alternatively, you can use the CLI:
# Replace <Elastic_Agent_IP> with your actual value
add audit syslogAction Elastic_Syslog_Server <Elastic_Agent_IP> -serverPort 9001 -logLevel ALL -transport TCP
- Navigate to Configuration > System > Auditing > Syslog and go to the Policies tab.
- Click Add, name it
Elastic_WAF_Policy, and select the server created in the previous step. - Set the Expression to
true. - Navigate to Configuration > System > Auditing > Syslog and select Global Bindings.
- Select APPFW_GLOBAL and bind the
Elastic_WAF_Policywith a priority of100.
Alternatively, you can use the CLI:
add audit syslogPolicy Elastic_WAF_Policy true Elastic_Syslog_Server
bind audit syslogGlobal -policyName Elastic_WAF_Policy -priority 100 -globalBindType APPFW_GLOBAL
The following resources provide additional information about Citrix WAF logging:
- How to Send Application Firewall Messages to a Separate Syslog Server (CTX138973)
- How to Send NetScaler Application Firewall Logs to Syslog Server (CTX483235)
- Web App Firewall logs | NetScaler Documentation
To install and configure the Citrix Web App Firewall integration, follow these steps:
- In Kibana, navigate to Management > Integrations.
- Search for Citrix Web App Firewall and select it.
- Click Add Citrix Web App Firewall.
- Choose the input type that matches your Citrix configuration (TCP, UDP, or Log file).
To collect logs over a TCP connection, configure the following settings:
- Listen Address (
tcp_host): The bind address to listen for TCP connections. Set to0.0.0.0to bind to all available interfaces. Default:localhost. - Listen Port (
tcp_port): The TCP port number to listen on. Default:9001. - Preserve original event (
preserve_original_event): If checked, a raw copy of the original event is stored in theevent.originalfield. Default:False. - Tags (
tags): Custom tags to append to the event. Default:['citrix_waf', 'forwarded']. - Processors (
processors): Add custom processors to reduce fields or enhance metadata before the data is sent to Elastic. See Processors for details. - SSL Configuration (
ssl): Configure SSL options if you are using encrypted transport. Refer to the SSL documentation for details. - Custom TCP Options (
tcp_options): Specify advanced settings such asmax_message_sizeorline_delimiter. - Timezone (
tz_offset): The IANA time zone or offset (for example,+0200) to use when interpreting syslog timestamps without a time zone. Default:UTC.
To collect logs over a UDP connection, configure the following settings:
- Listen Address (
udp_host): The bind address to listen for UDP connections. Set to0.0.0.0to bind to all available interfaces. Default:localhost. - Listen Port (
udp_port): The UDP port number to listen on. Default:9001. - Preserve original event (
preserve_original_event): If checked, a raw copy of the original event is stored in theevent.originalfield. Default:False. - Tags (
tags): Custom tags to append to the event. Default:['citrix_waf', 'forwarded']. - Processors (
processors): Add custom processors to filter or enhance the log data. See Processors for details. - Custom UDP Options (
udp_options): Specify advanced settings such asmax_message_sizeorread_buffer. - Timezone (
tz_offset): The IANA time zone or offset (for example,+0200) for logs without time zone information. Default:UTC.
To collect logs directly from files on the host where Elastic Agent is running, configure the following settings:
- Paths (
paths): A list of absolute paths to the log files. Default:['/var/log/citrix-waf.log']. - Preserve original event (
preserve_original_event): If checked, a raw copy of the original event is stored in theevent.originalfield. Default:False. - Tags (
tags): Custom tags to append to the event. Default:['citrix_waf', 'forwarded']. - Processors (
processors): Add custom processors for pre-processing logs on the agent. See Processors for details. - Timezone (
tz_offset): The IANA time zone or offset (for example,+0200) for logs without time zone information. Default:UTC.
After completing the configuration, assign the integration to an agent policy and click Save and continue.
To verify the integration is working correctly, follow these steps:
- Verify the Elastic Agent status:
- Navigate to Management > Fleet > Agents.
- Ensure the agent is in a
HealthyorOnlinestate.
- Trigger data flow on the Citrix WAF:
- Generate web traffic by accessing a web application protected by the Citrix WAF.
- Simulate a policy violation (for example,
curl http://<waf_app_ip>/etc/passwd) to trigger a block or log event. - Log in or out of the Citrix management interface to generate administrative audit logs.
- Check data in Kibana:
- Navigate to Analytics > Discover.
- Select the
logs-*data view. - Enter the KQL filter
data_stream.dataset : "citrix_waf.log"and confirm that logs appear with recent timestamps. - Verify that fields such as
event.dataset,source.ip,event.action, andmessageare populated correctly.
- Check Dashboards:
- Navigate to Analytics > Dashboards.
- Search for Citrix Web App Firewall to verify the pre-built visualizations are populating with data.
For help with Elastic ingest tools, check Common problems.
Address common configuration issues using the following guidance:
- CEF logging disabled: If logs appear in Kibana as a single unparsed string in the
messagefield, verify that CEF logging is enabled in the Citrix WAF engine settings. Without the CEF format, the parser can't identify specific security fields. - Global binding missing: If no logs are arriving at the Elastic Agent, verify the audit policy is bound to the
APPFW_GLOBALbind point. Binding toSYSTEM_GLOBALmight result in WAF logs being mixed with general system logs or suppressed depending on priority settings. - Port conflicts: Ensure that the
Listen Portconfigured in the integration settings (for example,9001) isn't being used by another service on the Elastic Agent host. You can use commands likenetstat -anoorss -tulpnto verify if the agent is listening on the expected port. - Firewall or network ACL blocks: Verify that any network firewalls between the Citrix appliance and the Elastic Agent permit traffic on the configured UDP or TCP port.
- Timestamp mismatches: If logs appear to be missing or have incorrect times, check for a significant time difference between the Citrix appliance and the Elastic Agent. Use the
Timezonesetting in the integration configuration to correct for offset differences. - Parsing failures: Check the
error.messagefield in Kibana for messages like "Provided grok patterns did not match". This usually indicates that the Citrix log format isn't standard CEF. Ensure no custom syslog headers are prepended to the CEF payload on the Citrix side. - Truncated logs: If logs are incomplete or missing data, check the
max_message_sizesetting in the TCP or UDP options. Large WAF events with many headers can exceed the default10KiBlimit.
For more information on architectures that can be used for scaling this integration, check the Ingest Architectures documentation.
To ensure optimal performance in high-volume security environments, you should consider the following configuration and deployment strategies:
- Use TCP for transport to ensure reliable delivery and support for encrypted transport using SSL/TLS. While UDP has lower overhead, it doesn't guarantee delivery in high-volume scenarios.
- Monitor your host's disk I/O performance if you're using the
logfileinput. You'll need to handle sustained write and read loads, and you should implement log rotation to prevent disk exhaustion. - Check that the
max_message_sizesetting is sufficient for your largest Common Event Format (CEF) payloads. The default is10KiB, and logs that exceed this size will be truncated. - Isolate Citrix Web App Firewall specific logs from general system logs by using the
-globalBindType APPFW_GLOBALcommand on your Citrix appliance. This reduces the processing overhead on the Elastic Agent. - Filter your logs at the source by configuring specific log levels. Focusing your collection on
NOTICEor higher severity events helps you avoid processing low-value debugging information. - Scale your deployment by using multiple Elastic Agents behind a network load balancer. It's best to place these agents in close network proximity to your Citrix appliances to minimize latency.
- Allocate sufficient CPU resources to your Elastic Agent hosts. High-velocity CEF data parsing and the use of complex processors can be CPU-intensive.
The following inputs are supported by this integration: These inputs can be used with this integration:
logfile
For more details about the logfile input settings, check the Filebeat documentation.
To collect logs via logfile, select Collect logs via the logfile input and configure the following parameter:
- Paths: List of glob-based paths to crawl and fetch log files from. Supports glob patterns like
/var/log/*.logor/var/log/*/*.logfor subfolder matching. Each file found starts a separate harvester.
tcp
For more details about the TCP input settings, check the Filebeat documentation.
To collect logs via TCP, select Collect logs via TCP and configure the following parameters:
Required Settings:
- Host
- Port
Common Optional Settings:
- Max Message Size - Maximum size of incoming messages
- Max Connections - Maximum number of concurrent connections
- Timeout - How long to wait for data before closing idle connections
- Line Delimiter - Character(s) that separate log messages
To enable encrypted connections, configure the following SSL settings:
SSL Settings:
- Enable SSL - Toggle to enable SSL/TLS encryption
- Certificate - Path to the SSL certificate file (
.crtor.pem) - Certificate Key - Path to the private key file (
.key) - Certificate Authorities - Path to CA certificate file for client certificate validation (optional)
- Client Authentication - Require client certificates (
none,optional, orrequired) - Supported Protocols - TLS versions to support (e.g.,
TLSv1.2,TLSv1.3)
Example SSL Configuration:
ssl.enabled: true
ssl.certificate: "/path/to/server.crt"
ssl.key: "/path/to/server.key"
ssl.certificate_authorities: ["/path/to/ca.crt"]
ssl.client_authentication: "optional"
udp
For more details about the UDP input settings, check the Filebeat documentation.
To collect logs via UDP, select Collect logs via UDP and configure the following parameters:
Required Settings:
- Host
- Port
Common Optional Settings:
- Max Message Size - Maximum size of UDP packets to accept (default: 10KB, max: 64KB)
- Read Buffer - UDP socket read buffer size for handling bursts of messages
- Read Timeout - How long to wait for incoming packets before checking for shutdown
This integration includes the following data stream:
The log data stream provides events from Citrix Web App Firewall of the following types: security violation logs, policy match logs, and system audit logs. It supports logs in both standard syslog format and Common Event Format (CEF).
The following fields are exported by this data stream: Exported fields
| Field | Description | Type |
|---|---|---|
| @timestamp | Date/time when the event originated. This is the date/time extracted from the event, typically representing when the event was generated by the source. If the event source has no original timestamp, this value is typically populated by the first time the event was received by the pipeline. Required field for all events. | date |
| citrix.cef_format | Whether the logging is in Citrix CEF format. | boolean |
| citrix.cef_version | The CEF format version used in the logs. | keyword |
| citrix.default_class | Whether the event class was the default. | boolean |
| citrix.detail | The CEF or Citrix Native format details for the event. | keyword |
| citrix.device_event_class_id | The ID of the event class. | keyword |
| citrix.device_product | The model of the appliance. | keyword |
| citrix.device_vendor | The name of the vendor for the device. | keyword |
| citrix.device_version | The version of the device. | keyword |
| citrix.extended | Additional data associated with the event. | flattened |
| citrix.facility | The logging facility. | keyword |
| citrix.host | The name of the host receiving the logs. | keyword |
| citrix.name | The name of the security check. | keyword |
| citrix.ppe_id | Packet Processing Engine ID. | keyword |
| citrix.priority | The logging priority. | keyword |
| citrix.profile_name | The name of the profile that raised the event. | keyword |
| citrix.session_id | The ID for the session. | keyword |
| citrix.severity | The severity of the event. | keyword |
| citrix.signature_violation_category | The category that the violation is grouped into. | keyword |
| client.address | Some event client addresses are defined ambiguously. The event will sometimes list an IP, a domain or a unix socket. You should always store the raw address in the .address field. Then it should be duplicated to .ip or .domain, depending on which one it is. |
keyword |
| client.as.number | Unique number allocated to the autonomous system. The autonomous system number (ASN) uniquely identifies each network on the Internet. | long |
| client.as.organization.name | Organization name. | keyword |
| client.as.organization.name.text | Multi-field of client.as.organization.name. |
match_only_text |
| client.domain | The domain name of the client system. This value may be a host name, a fully qualified domain name, or another host naming format. The value may derive from the original event or be added from enrichment. | keyword |
| client.geo.city_name | City name. | keyword |
| client.geo.continent_name | Name of the continent. | keyword |
| client.geo.country_iso_code | Country ISO code. | keyword |
| client.geo.country_name | Country name. | keyword |
| client.geo.location | Longitude and latitude. | geo_point |
| client.geo.region_iso_code | Region ISO code. | keyword |
| client.geo.region_name | Region name. | keyword |
| client.ip | IP address of the client (IPv4 or IPv6). | ip |
| client.port | Port of the client. | long |
| client.user.name | Short name or login of the user. | keyword |
| client.user.name.text | Multi-field of client.user.name. |
match_only_text |
| cloud.account.id | The cloud account or organization id used to identify different entities in a multi-tenant environment. Examples: AWS account id, Google Cloud ORG Id, or other unique identifier. | keyword |
| cloud.availability_zone | Availability zone in which this host is running. | keyword |
| cloud.image.id | Image ID for the cloud instance. | keyword |
| cloud.instance.id | Instance ID of the host machine. | keyword |
| cloud.instance.name | Instance name of the host machine. | keyword |
| cloud.machine.type | Machine type of the host machine. | keyword |
| cloud.project.id | Name of the project in Google Cloud. | keyword |
| cloud.provider | Name of the cloud provider. Example values are aws, azure, gcp, or digitalocean. | keyword |
| cloud.region | Region in which this host is running. | keyword |
| container.id | Unique container id. | keyword |
| container.image.name | Name of the image the container was built on. | keyword |
| container.labels | Image labels. | object |
| container.name | Container name. | keyword |
| data_stream.dataset | Data stream dataset. | constant_keyword |
| data_stream.namespace | Data stream namespace. | constant_keyword |
| data_stream.type | Data stream type. | constant_keyword |
| ecs.version | ECS version this event conforms to. ecs.version is a required field and must exist in all events. When querying across multiple indices -- which may conform to slightly different ECS versions -- this field lets integrations adjust to the schema version of the events. |
keyword |
| error.message | Error message. | match_only_text |
| event.category | This is one of four ECS Categorization Fields, and indicates the second level in the ECS category hierarchy. event.category represents the "big buckets" of ECS categories. For example, filtering on event.category:process yields all events relating to process activity. This field is closely related to event.type, which is used as a subcategory. This field is an array. This will allow proper categorization of some events that fall in multiple categories. |
keyword |
| event.code | Identification code for this event, if one exists. Some event sources use event codes to identify messages unambiguously, regardless of message language or wording adjustments over time. An example of this is the Windows Event ID. | keyword |
| event.created | event.created contains the date/time when the event was first read by an agent, or by your pipeline. This field is distinct from @timestamp in that @timestamp typically contain the time extracted from the original event. In most situations, these two timestamps will be slightly different. The difference can be used to calculate the delay between your source generating an event, and the time when your agent first processed it. This can be used to monitor your agent's or pipeline's ability to keep up with your event source. In case the two timestamps are identical, @timestamp should be used. |
date |
| event.dataset | Event dataset | constant_keyword |
| event.duration | Duration of the event in nanoseconds. If event.start and event.end are known this value should be the difference between the end and start time. |
long |
| event.end | event.end contains the date when the event ended or when the activity was last observed. |
date |
| event.ingested | Timestamp when an event arrived in the central data store. This is different from @timestamp, which is when the event originally occurred. It's also different from event.created, which is meant to capture the first time an agent saw the event. In normal conditions, assuming no tampering, the timestamps should chronologically look like this: @timestamp < event.created < event.ingested. |
date |
| event.kind | This is one of four ECS Categorization Fields, and indicates the highest level in the ECS category hierarchy. event.kind gives high-level information about what type of information the event contains, without being specific to the contents of the event. For example, values of this field distinguish alert events from metric events. The value of this field can be used to inform how these kinds of events should be handled. They may warrant different retention, different access control, it may also help understand whether the data is coming in at a regular interval or not. |
keyword |
| event.module | Event module | constant_keyword |
| event.provider | Source of the event. Event transports such as Syslog or the Windows Event Log typically mention the source of an event. It can be the name of the software that generated the event (e.g. Sysmon, httpd), or of a subsystem of the operating system (kernel, Microsoft-Windows-Security-Auditing). | keyword |
| event.severity | The numeric severity of the event according to your event source. What the different severity values mean can be different between sources and use cases. It's up to the implementer to make sure severities are consistent across events from the same source. The Syslog severity belongs in log.syslog.severity.code. event.severity is meant to represent the severity according to the event source (e.g. firewall, IDS). If the event source does not publish its own severity, you may optionally copy the log.syslog.severity.code to event.severity. |
long |
| event.start | event.start contains the date when the event started or when the activity was first observed. |
date |
| event.timezone | This field should be populated when the event's timestamp does not include timezone information already (e.g. default Syslog timestamps). It's optional otherwise. Acceptable timezone formats are: a canonical ID (e.g. "Europe/Amsterdam"), abbreviated (e.g. "EST") or an HH:mm differential (e.g. "-05:00"). | keyword |
| event.type | This is one of four ECS Categorization Fields, and indicates the third level in the ECS category hierarchy. event.type represents a categorization "sub-bucket" that, when used along with the event.category field values, enables filtering events down to a level appropriate for single visualization. This field is an array. This will allow proper categorization of some events that fall in multiple event types. |
keyword |
| file.path | Full path to the file, including the file name. It should include the drive letter, when appropriate. | keyword |
| file.path.text | Multi-field of file.path. |
match_only_text |
| host.architecture | Operating system architecture. | keyword |
| host.containerized | If the host is a container. | boolean |
| host.domain | Name of the domain of which the host is a member. For example, on Windows this could be the host's Active Directory domain or NetBIOS domain name. For Linux this could be the domain of the host's LDAP provider. | keyword |
| host.hostname | Hostname of the host. It normally contains what the hostname command returns on the host machine. |
keyword |
| host.id | Unique host id. As hostname is not always unique, use values that are meaningful in your environment. Example: The current usage of beat.name. |
keyword |
| host.ip | Host ip addresses. | ip |
| host.mac | Host mac addresses. | keyword |
| host.name | Name of the host. It can contain what hostname returns on Unix systems, the fully qualified domain name, or a name specified by the user. The sender decides which value to use. |
keyword |
| host.os.build | OS build information. | keyword |
| host.os.codename | OS codename, if any. | keyword |
| host.os.family | OS family (such as redhat, debian, freebsd, windows). | keyword |
| host.os.kernel | Operating system kernel version as a raw string. | keyword |
| host.os.name | Operating system name, without the version. | keyword |
| host.os.name.text | Multi-field of host.os.name. |
text |
| host.os.platform | Operating system platform (such centos, ubuntu, windows). | keyword |
| host.os.version | Operating system version as a raw string. | keyword |
| host.type | Type of host. For Cloud providers this can be the machine type like t2.medium. If vm, this could be the container, for example, or other information meaningful in your environment. |
keyword |
| http.request.id | A unique identifier for each HTTP request to correlate logs between clients and servers in transactions. The id may be contained in a non-standard HTTP header, such as X-Request-ID or X-Correlation-ID. |
keyword |
| http.request.method | HTTP request method. The value should retain its casing from the original event. For example, GET, get, and GeT are all considered valid values for this field. |
keyword |
| input.type | Input type. | keyword |
| labels | Custom key/value pairs. Can be used to add meta information to events. Should not contain nested objects. All values are stored as keyword. Example: docker and k8s labels. |
object |
| log.file.path | Full path to the log file this event came from, including the file name. It should include the drive letter, when appropriate. If the event wasn't read from a log file, do not populate this field. | keyword |
| log.level | Original log level of the log event. If the source of the event provides a log level or textual severity, this is the one that goes in log.level. If your source doesn't specify one, you may put your event transport's severity here (e.g. Syslog severity). Some examples are warn, err, i, informational. |
keyword |
| log.offset | Offset of the entry in the log file. | long |
| log.source.address | Source address from which the log event was read / sent from. | keyword |
| message | For log events the message field contains the log message, optimized for viewing in a log viewer. For structured logs without an original message field, other fields can be concatenated to form a human-readable summary of the event. If multiple messages exist, they can be combined into one message. | match_only_text |
| network.bytes | Total bytes transferred in both directions. If source.bytes and destination.bytes are known, network.bytes is their sum. |
long |
| network.community_id | A hash of source and destination IPs and ports, as well as the protocol used in a communication. This is a tool-agnostic standard to identify flows. Learn more at https://github.com/corelight/community-id-spec. | keyword |
| network.direction | Direction of the network traffic. When mapping events from a host-based monitoring context, populate this field from the host's point of view, using the values "ingress" or "egress". When mapping events from a network or perimeter-based monitoring context, populate this field from the point of view of the network perimeter, using the values "inbound", "outbound", "internal" or "external". Note that "internal" is not crossing perimeter boundaries, and is meant to describe communication between two hosts within the perimeter. Note also that "external" is meant to describe traffic between two hosts that are external to the perimeter. This could for example be useful for ISPs or VPN service providers. | keyword |
| network.iana_number | IANA Protocol Number (https://www.iana.org/assignments/protocol-numbers/protocol-numbers.xhtml). Standardized list of protocols. This aligns well with NetFlow and sFlow related logs which use the IANA Protocol Number. | keyword |
| network.inner | Network.inner fields are added in addition to network.vlan fields to describe the innermost VLAN when q-in-q VLAN tagging is present. Allowed fields include vlan.id and vlan.name. Inner vlan fields are typically used when sending traffic with multiple 802.1q encapsulations to a network sensor (e.g. Zeek, Wireshark.) | group |
| network.inner.vlan.id | VLAN ID as reported by the observer. | keyword |
| network.inner.vlan.name | Optional VLAN name as reported by the observer. | keyword |
| network.protocol | In the OSI Model this would be the Application Layer protocol. For example, http, dns, or ssh. The field value must be normalized to lowercase for querying. |
keyword |
| network.transport | Same as network.iana_number, but instead using the Keyword name of the transport layer (udp, tcp, ipv6-icmp, etc.) The field value must be normalized to lowercase for querying. | keyword |
| network.type | In the OSI Model this would be the Network Layer. ipv4, ipv6, ipsec, pim, etc The field value must be normalized to lowercase for querying. | keyword |
| observer.egress.interface.name | Interface name as reported by the system. | keyword |
| observer.egress.zone | Network zone of outbound traffic as reported by the observer to categorize the destination area of egress traffic, e.g. Internal, External, DMZ, HR, Legal, etc. | keyword |
| observer.hostname | Hostname of the observer. | keyword |
| observer.ingress.interface.name | Interface name as reported by the system. | keyword |
| observer.ingress.zone | Network zone of incoming traffic as reported by the observer to categorize the source area of ingress traffic. e.g. internal, External, DMZ, HR, Legal, etc. | keyword |
| observer.ip | IP addresses of the observer. | ip |
| observer.name | Custom name of the observer. This is a name that can be given to an observer. This can be helpful for example if multiple firewalls of the same model are used in an organization. If no custom name is needed, the field can be left empty. | keyword |
| observer.product | The product name of the observer. | keyword |
| observer.type | The type of the observer the data is coming from. There is no predefined list of observer types. Some examples are forwarder, firewall, ids, ips, proxy, poller, sensor, APM server. |
keyword |
| observer.vendor | Vendor name of the observer. | keyword |
| observer.version | Observer version. | keyword |
| process.name | Process name. Sometimes called program name or similar. | keyword |
| process.name.text | Multi-field of process.name. |
match_only_text |
| process.pid | Process id. | long |
| related.hosts | All hostnames or other host identifiers seen on your event. Example identifiers include FQDNs, domain names, workstation names, or aliases. | keyword |
| related.ip | All of the IPs seen on your event. | ip |
| related.user | All the user names or other user identifiers seen on the event. | keyword |
| server.address | Some event server addresses are defined ambiguously. The event will sometimes list an IP, a domain or a unix socket. You should always store the raw address in the .address field. Then it should be duplicated to .ip or .domain, depending on which one it is. |
keyword |
| server.domain | The domain name of the server system. This value may be a host name, a fully qualified domain name, or another host naming format. The value may derive from the original event or be added from enrichment. | keyword |
| server.ip | IP address of the server (IPv4 or IPv6). | ip |
| server.port | Port of the server. | long |
| server.user.name | Short name or login of the user. | keyword |
| server.user.name.text | Multi-field of server.user.name. |
match_only_text |
| source.address | Some event source addresses are defined ambiguously. The event will sometimes list an IP, a domain or a unix socket. You should always store the raw address in the .address field. Then it should be duplicated to .ip or .domain, depending on which one it is. |
keyword |
| source.as.number | Unique number allocated to the autonomous system. The autonomous system number (ASN) uniquely identifies each network on the Internet. | long |
| source.as.organization.name | Organization name. | keyword |
| source.as.organization.name.text | Multi-field of source.as.organization.name. |
match_only_text |
| source.bytes | Bytes sent from the source to the destination. | long |
| source.domain | The domain name of the source system. This value may be a host name, a fully qualified domain name, or another host naming format. The value may derive from the original event or be added from enrichment. | keyword |
| source.geo.city_name | City name. | keyword |
| source.geo.continent_name | Name of the continent. | keyword |
| source.geo.country_iso_code | Country ISO code. | keyword |
| source.geo.country_name | Country name. | keyword |
| source.geo.location | Longitude and latitude. | geo_point |
| source.geo.region_iso_code | Region ISO code. | keyword |
| source.geo.region_name | Region name. | keyword |
| source.ip | IP address of the source (IPv4 or IPv6). | ip |
| source.nat.ip | Translated ip of source based NAT sessions (e.g. internal client to internet) Typically connections traversing load balancers, firewalls, or routers. | ip |
| source.nat.port | Translated port of source based NAT sessions. (e.g. internal client to internet) Typically used with load balancers, firewalls, or routers. | long |
| source.port | Port of the source. | long |
| source.user.domain | Name of the directory the user is a member of. For example, an LDAP or Active Directory domain name. | keyword |
| source.user.group.name | Name of the group. | keyword |
| source.user.name | Short name or login of the user. | keyword |
| source.user.name.text | Multi-field of source.user.name. |
match_only_text |
| tags | List of keywords used to tag each event. | keyword |
| url.domain | Domain of the url, such as "www.elastic.co". In some cases a URL may refer to an IP and/or port directly, without a domain name. In this case, the IP address would go to the domain field. If the URL contains a literal IPv6 address enclosed by [ and ] (IETF RFC 2732), the [ and ] characters should also be captured in the domain field. |
keyword |
| url.extension | The field contains the file extension from the original request url, excluding the leading dot. The file extension is only set if it exists, as not every url has a file extension. The leading period must not be included. For example, the value must be "png", not ".png". Note that when the file name has multiple extensions (example.tar.gz), only the last one should be captured ("gz", not "tar.gz"). | keyword |
| url.fragment | Portion of the url after the #, such as "top". The # is not part of the fragment. |
keyword |
| url.full | If full URLs are important to your use case, they should be stored in url.full, whether this field is reconstructed or present in the event source. |
wildcard |
| url.full.text | Multi-field of url.full. |
match_only_text |
| url.original | Unmodified original url as seen in the event source. Note that in network monitoring, the observed URL may be a full URL, whereas in access logs, the URL is often just represented as a path. This field is meant to represent the URL as it was observed, complete or not. | wildcard |
| url.original.text | Multi-field of url.original. |
match_only_text |
| url.password | Password of the request. | keyword |
| url.path | Path of the request, such as "/search". | wildcard |
| url.port | Port of the request, such as 443. | long |
| url.query | The query field describes the query string of the request, such as "q=elasticsearch". The ? is excluded from the query string. If a URL contains no ?, there is no query field. If there is a ? but no query, the query field exists with an empty string. The exists query can be used to differentiate between the two cases. |
keyword |
| url.registered_domain | The highest registered url domain, stripped of the subdomain. For example, the registered domain for "foo.example.com" is "example.com". This value can be determined precisely with a list like the public suffix list (https://publicsuffix.org). Trying to approximate this by simply taking the last two labels will not work well for TLDs such as "co.uk". | keyword |
| url.scheme | Scheme of the request, such as "https". Note: The : is not part of the scheme. |
keyword |
| url.subdomain | The subdomain portion of a fully qualified domain name includes all of the names except the host name under the registered_domain. In a partially qualified domain, or if the the qualification level of the full name cannot be determined, subdomain contains all of the names below the registered domain. For example the subdomain portion of "www.east.example.com" is "east". If the domain has multiple levels of subdomain, such as "sub2.sub1.example.com", the subdomain field should contain "sub2.sub1", with no trailing period. | keyword |
| url.top_level_domain | The effective top level domain (eTLD), also known as the domain suffix, is the last part of the domain name. For example, the top level domain for example.com is "com". This value can be determined precisely with a list like the public suffix list (https://publicsuffix.org). Trying to approximate this by simply taking the last label will not work well for effective TLDs such as "co.uk". | keyword |
| url.username | Username of the request. | keyword |
| user.email | User email address. | keyword |
| user.name | Short name or login of the user. | keyword |
| user.name.text | Multi-field of user.name. |
match_only_text |
Example
{
"@timestamp": "2012-12-18T21:46:17.000Z",
"agent": {
"ephemeral_id": "9153862d-f83f-4bd1-bbc9-c3ff3d96e726",
"id": "e30119bc-b47d-4e56-86e3-4a9683305c6e",
"name": "docker-fleet-agent",
"type": "filebeat",
"version": "8.2.3"
},
"citrix": {
"cef_format": true,
"cef_version": "0",
"detail": "CEF:0|Citrix|NetScaler|NS10.0|APPFW|APPFW_STARTURL|6|src=175.16.199.1 spt=54711 method=GET request=http://vpx247.example.net/FFC/login_post.html?abc\\=def msg=Disallow Illegal URL. cn1=465 cn2=535 cs1=profile1 cs2=PPE0 cs3=IliG4Dxp1SjOhKVRDVBXmqvAaIcA000 cs4=ALERT cs5=2012 act=not blocked",
"device_event_class_id": "APPFW",
"device_product": "NetScaler",
"device_vendor": "Citrix",
"device_version": "NS10.0",
"facility": "local0",
"name": "APPFW_STARTURL",
"ppe_id": "PPE0",
"priority": "info",
"profile_name": "profile1",
"session_id": "IliG4Dxp1SjOhKVRDVBXmqvAaIcA000",
"severity": "ALERT"
},
"client": {
"geo": {
"city_name": "London",
"continent_name": "Europe",
"country_iso_code": "GB",
"country_name": "United Kingdom",
"location": {
"lat": 51.5142,
"lon": -0.0931
},
"region_iso_code": "GB-ENG",
"region_name": "England"
},
"ip": "81.2.69.144"
},
"data_stream": {
"dataset": "citrix_waf.log",
"namespace": "ep",
"type": "logs"
},
"ecs": {
"version": "8.17.0"
},
"elastic_agent": {
"id": "e30119bc-b47d-4e56-86e3-4a9683305c6e",
"snapshot": false,
"version": "8.2.3"
},
"event": {
"action": "not blocked",
"agent_id_status": "verified",
"dataset": "citrix_waf.log",
"id": "465",
"ingested": "2022-07-12T00:06:17Z",
"original": "Dec 18 21:46:17 <local0.info> 81.2.69.144 CEF:0|Citrix|NetScaler|NS10.0|APPFW|APPFW_STARTURL|6|src=175.16.199.1 spt=54711 method=GET request=http://vpx247.example.net/FFC/login_post.html?abc\\=def msg=Disallow Illegal URL. cn1=465 cn2=535 cs1=profile1 cs2=PPE0 cs3=IliG4Dxp1SjOhKVRDVBXmqvAaIcA000 cs4=ALERT cs5=2012 act=not blocked",
"severity": 6,
"timezone": "+00:00"
},
"http": {
"request": {
"id": "535",
"method": "GET"
}
},
"input": {
"type": "tcp"
},
"log": {
"source": {
"address": "172.22.0.4:41588"
}
},
"message": "Disallow Illegal URL.",
"source": {
"geo": {
"city_name": "Changchun",
"continent_name": "Asia",
"country_iso_code": "CN",
"country_name": "China",
"location": {
"lat": 43.88,
"lon": 125.3228
},
"region_iso_code": "CN-22",
"region_name": "Jilin Sheng"
},
"ip": "175.16.199.1",
"port": 54711
},
"tags": [
"preserve_original_event",
"citrix_waf",
"forwarded"
],
"url": {
"domain": "vpx247.example.net",
"extension": "html",
"original": "http://vpx247.example.net/FFC/login_post.html?abc\\=def",
"path": "/FFC/login_post.html",
"query": "abc\\=def",
"scheme": "http"
}
}
For more information about Citrix Web App Firewall logs and configuration, refer to the following vendor resources:
- Web App Firewall logs - NetScaler Documentation
- NetScaler AppFirewall: Configuration, CEF logging, Signatures
- Send logs to external syslog server
- Citrix ADC Auditing Policies
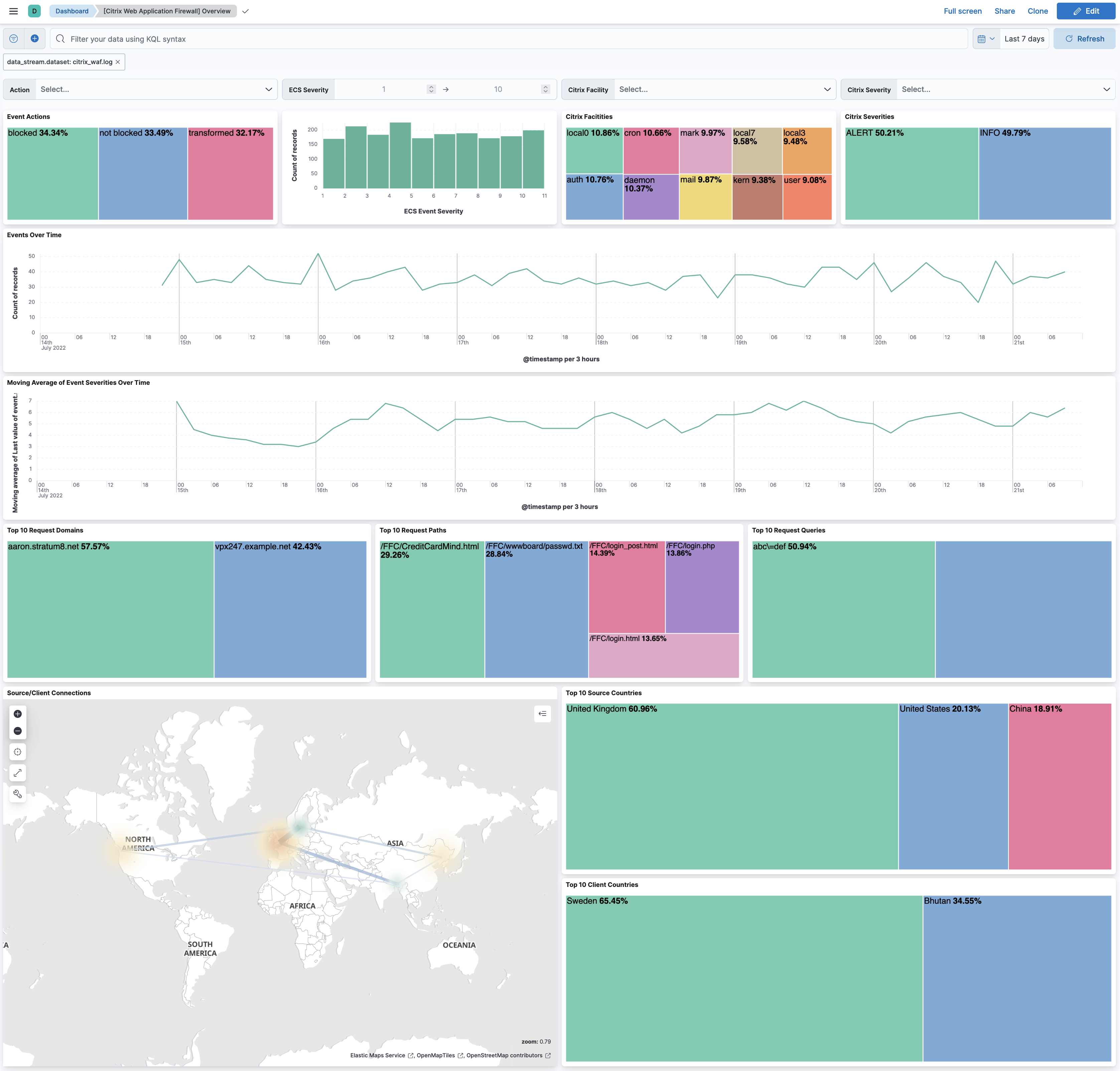
This integration includes one or more Kibana dashboards that visualizes the data collected by the integration. The screenshots below illustrate how the ingested data is displayed.
Changelog
| Version | Details | Minimum Kibana version |
|---|---|---|
| 1.20.0 | Enhancement (View pull request) Update documentation for the integration. |
9.0.0 8.11.0 |
| 1.19.0 | Enhancement (View pull request) Preserve event.original on pipeline error. |
9.0.0 8.11.0 |
| 1.18.3 | Enhancement (View pull request) Generate processor tags and normalize error handler. |
9.0.0 8.11.0 |
| 1.18.2 | Bug fix (View pull request) Fix service names in documentation. |
9.0.0 8.11.0 |
| 1.18.1 | Enhancement (View pull request) Changed owners. |
9.0.0 8.11.0 |
| 1.18.0 | Enhancement (View pull request) Support stack version 9.0. |
9.0.0 8.11.0 |
| 1.17.1 | Bug fix (View pull request) Updated SSL description to be uniform and to include links to documentation. |
8.11.0 |
| 1.17.0 | Enhancement (View pull request) ECS version updated to 8.17.0. |
8.11.0 |
| 1.16.1 | Bug fix (View pull request) Use triple-brace Mustache templating when referencing variables in ingest pipelines. |
8.11.0 |
| 1.16.0 | Enhancement (View pull request) Allow @custom pipeline access to event.original without setting preserve_original_event. |
8.11.0 |
| 1.15.0 | Enhancement (View pull request) Relax message header parsing constraints. |
8.3.0 |
| 1.14.0 | Enhancement (View pull request) Update package spec to 3.0.3. |
8.3.0 |
| 1.13.2 | Enhancement (View pull request) Changed owners |
8.3.0 |
| 1.13.1 | Bug fix (View pull request) Fix exclude_files pattern. |
8.3.0 |
| 1.13.0 | Enhancement (View pull request) ECS version updated to 8.11.0. |
8.3.0 |
| 1.12.0 | Enhancement (View pull request) Improve 'event.original' check to avoid errors if set. |
8.3.0 |
| 1.11.1 | Bug fix (View pull request) Fix mappings of empty groups imported from ECS |
8.3.0 |
| 1.11.0 | Enhancement (View pull request) ECS version updated to 8.10.0. |
8.3.0 |
| 1.10.0 | Enhancement (View pull request) The format_version in the package manifest changed from 2.11.0 to 3.0.0. Removed dotted YAML keys from package manifest. Added 'owner.type: elastic' to package manifest. |
8.3.0 |
| 1.9.0 | Enhancement (View pull request) Add tags.yml file so that integration's dashboards and saved searches are tagged with "Security Solution" and displayed in the Security Solution UI. |
8.3.0 |
| 1.8.0 | Enhancement (View pull request) Update package to ECS 8.9.0. |
8.3.0 |
| 1.7.0 | Enhancement (View pull request) Ensure event.kind is correctly set for pipeline errors. |
8.3.0 |
| 1.6.0 | Enhancement (View pull request) Update package to ECS 8.8.0. |
8.3.0 |
| 1.5.0 | Enhancement (View pull request) Update package-spec version to 2.7.0. |
8.3.0 |
| 1.4.0 | Enhancement (View pull request) Update package to ECS 8.7.0. |
8.3.0 |
| 1.3.1 | Enhancement (View pull request) Added categories and/or subcategories. |
8.3.0 |
| 1.3.0 | Enhancement (View pull request) Update package to ECS 8.6.0. |
8.3.0 |
| 1.2.0 | Enhancement (View pull request) Update package to ECS 8.5.0. |
8.3.0 |
| 1.1.2 | Bug fix (View pull request) Remove duplicate fields. |
8.3.0 |
| 1.1.1 | Enhancement (View pull request) Use ECS geo.location definition. |
8.3.0 |
| 1.1.0 | Enhancement (View pull request) Update package to ECS 8.4.0 |
8.3.0 |
| 1.0.0 | Enhancement (View pull request) Add dashboard. Bug fix (View pull request) Add missing client.as field mappings. Bug fix (View pull request) Remove unused destination field mappings. |
8.3.0 |
| 0.1.1 | Bug fix (View pull request) Fix UDP parameter name and remove setting from default. |
8.2.0 |
| 0.1.0 | Enhancement (View pull request) Initial draft of the package |
— |