Detections prerequisites and requirements
editDetections prerequisites and requirements
editTo use the Detections feature, you first need to configure a few settings. You also need the appropriate license to send notifications when detection alerts are generated.
Several steps are only required for self-managed Elastic Stack deployments. If you’re using an Elastic Cloud deployment, you only need to enable detections.
Additionally, there are some advanced settings used to configure Kibana value list upload limits.
Configure self-managed Elastic Stack deployments
editThese steps are only required for self-managed deployments:
- HTTPS must be configured for communication between Elasticsearch and Kibana.
-
In the
elasticsearch.ymlconfiguration file, set thexpack.security.enabledsetting totrue. For more information, refer to Configuring Elasticsearch and Security settings in Elasticsearch. -
In the
kibana.ymlconfiguration file, add thexpack.encryptedSavedObjects.encryptionKeysetting with any alphanumeric value of at least 32 characters. For example:xpack.encryptedSavedObjects.encryptionKey: 'fhjskloppd678ehkdfdlliverpoolfcr'
After changing the xpack.encryptedSavedObjects.encryptionKey value
and restarting Kibana, you must restart all detection rules.
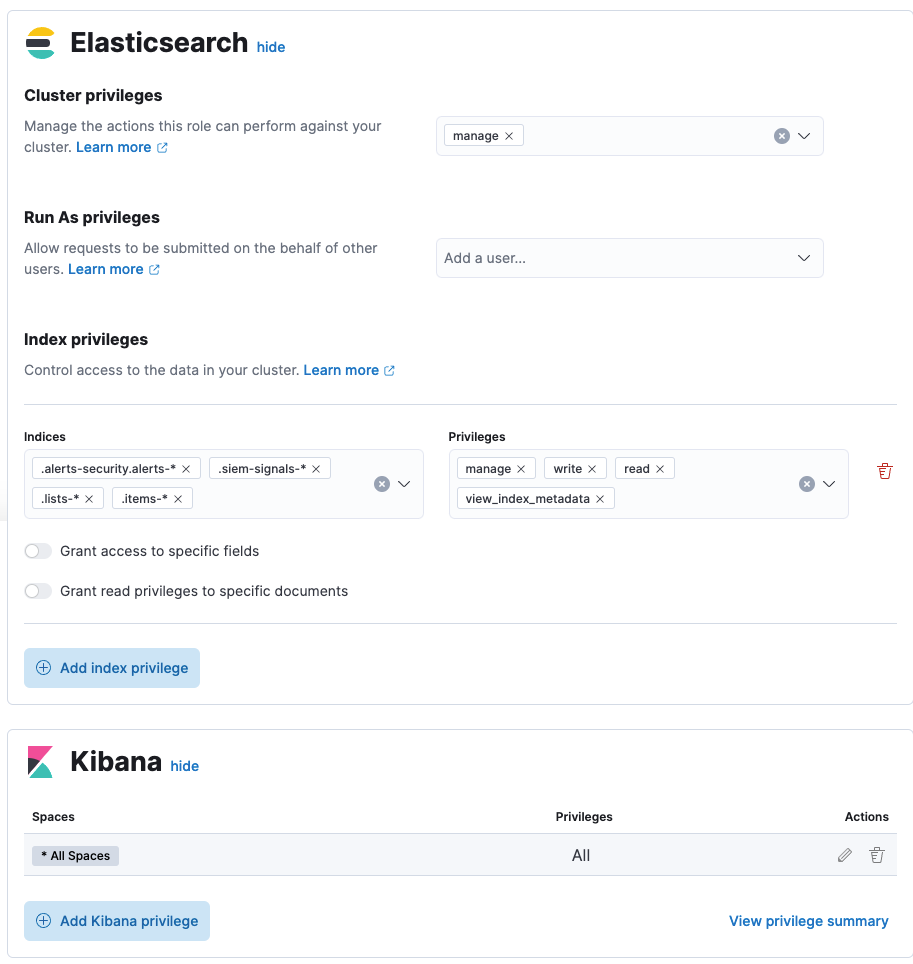
Enable and access detections
editTo use the Detections feature, it must be enabled and your role must have access to rules and alerts. If your role does not have the cluster and index privileges needed to enable this feature, you can request someone who has these privileges to visit your Kibana space, which will turn it on for you. The following table describes the required privileges to access the Detections page, including rules and alerts.
For instructions about using Machine Learning jobs and rules, refer to Machine learning job and rule requirements.
In Elastic Stack version 8.0.0, the .siem-signals-<space-id> index was renamed to .alerts-security.alerts-<space-id>. If you’re upgrading to 8.0.0 or later, users should have privileges for the .alerts-security.alerts-<space-id> AND .siem-signals-<space-id> indices. If you’re newly installing the Elastic Stack, then users do not need privileges for the .siem-signals-<space-id> index.
| Action | Cluster Privileges | Index Privileges | Kibana Privileges |
|---|---|---|---|
Enable the Detections feature in your Kibana space |
The |
The
1 NOTE: If you’re upgrading to Elastic Stack 8.0.0 or later, users should have privileges for the |
Kibana space |
Enable the Detections feature in all Kibana spaces NOTE: To turn on the Detections feature, visit the Detections page for each appropriate Kibana space. |
The |
The
1 NOTE: If you’re upgrading to Elastic Stack 8.0.0 or later, users should have privileges for the |
Kibana space |
Preview rules |
N/A |
The
|
Kibana space |
Manage rules |
N/A |
The
1 NOTE: If you’re upgrading to Elastic Stack 8.0.0 or later, users should have privileges for the |
Kibana space NOTE: You need additional
|
Manage alerts NOTE: Allows you to manage alerts, but not modify rules. |
N/A |
The
1 NOTE: If you’re upgrading to Elastic Stack 8.0.0 or later, users should have privileges for the |
Kibana space |
Create the NOTE: To initiate the process that creates the |
The |
The
|
Kibana space |
Here is an example of a user who has the Detections feature enabled in all Kibana spaces:
Authorization
editRules, including all background detection and the actions they generate, are authorized using an API key associated with the last user to edit the rule. Upon creating or modifying a rule, an API key is generated for that user, capturing a snapshot of their privileges. The API key is then used to run all background tasks associated with the rule including detection checks and executing actions.
If a rule requires certain privileges to run, such as index privileges, keep in mind that if a user without those privileges updates the rule, the rule will no longer function.
Configure list upload limits
editYou can set limits to the number of bytes and the buffer size used to upload value lists to Elastic Security.
To set the value:
-
Open
kibana.ymlconfiguration file or edit your Kibana cloud instance. -
Add any of these settings and their required values:
-
xpack.lists.maxImportPayloadBytes: Sets the number of bytes allowed for uploading Elastic Security value lists (default9000000, maximum100000000). For every 10 megabytes, it is recommended to have an additional 1 gigabyte of RAM reserved for Kibana.For example, on a Kibana instance with 2 gigabytes of RAM, you can set this value up to 20000000 (20 megabytes).
-
xpack.lists.importBufferSize: Sets the buffer size used for uploading Elastic Security value lists (default1000). Change the value if you’re experiencing slow upload speeds or larger than wanted memory usage when uploading value lists. Set to a higher value to increase throughput at the expense of using more Kibana memory, or a lower value to decrease throughput and reduce memory usage.
-
For information on how to configure Elastic Cloud deployments, refer to Add Kibana user settings.