- Elastic Security: other versions:
- Elastic Security overview
- What’s new
- Get started with Elastic Security
- Elastic Security UI
- Anomaly Detection with Machine Learning
- Detections and alerts
- Create a detection rule
- Manage detection rules
- Monitor and troubleshoot rule executions
- Rule exceptions and value lists
- About building-block rules
- Managing detection alerts
- Visual event analyzer
- Tune detection rules
- Prebuilt rule changes per release
- Prebuilt rule reference
- AWS Access Secret in Secrets Manager
- AWS CloudTrail Log Created
- AWS CloudTrail Log Deleted
- AWS CloudTrail Log Suspended
- AWS CloudTrail Log Updated
- AWS CloudWatch Alarm Deletion
- AWS CloudWatch Log Group Deletion
- AWS CloudWatch Log Stream Deletion
- AWS Config Service Tampering
- AWS Configuration Recorder Stopped
- AWS EC2 Encryption Disabled
- AWS EC2 Flow Log Deletion
- AWS EC2 Network Access Control List Creation
- AWS EC2 Network Access Control List Deletion
- AWS EC2 Snapshot Activity
- AWS Execution via System Manager
- AWS GuardDuty Detector Deletion
- AWS IAM Assume Role Policy Update
- AWS IAM Brute Force of Assume Role Policy
- AWS IAM Deactivation of MFA Device
- AWS IAM Group Creation
- AWS IAM Group Deletion
- AWS IAM Password Recovery Requested
- AWS IAM User Addition to Group
- AWS Management Console Brute Force of Root User Identity
- AWS Management Console Root Login
- AWS RDS Cluster Creation
- AWS RDS Cluster Deletion
- AWS RDS Instance/Cluster Stoppage
- AWS Root Login Without MFA
- AWS S3 Bucket Configuration Deletion
- AWS WAF Access Control List Deletion
- AWS WAF Rule or Rule Group Deletion
- Abnormally Large DNS Response
- Access of Stored Browser Credentials
- Access to Keychain Credentials Directories
- AdFind Command Activity
- Adding Hidden File Attribute via Attrib
- Administrator Privileges Assigned to an Okta Group
- Administrator Role Assigned to an Okta User
- Adobe Hijack Persistence
- Adversary Behavior - Detected - Elastic Endgame
- Anomalous Kernel Module Activity
- Anomalous Linux Compiler Activity
- Anomalous Process For a Linux Population
- Anomalous Process For a Windows Population
- Anomalous Windows Process Creation
- Apple Script Execution followed by Network Connection
- Apple Scripting Execution with Administrator Privileges
- Application Added to Google Workspace Domain
- Dumping Account Hashes via Built-In Commands
- Dumping of Keychain Content via Security Command
- EggShell Backdoor Execution
- Emond Rules Creation or Modification
- Encoded Executable Stored in the Registry
- Encoding or Decoding Files via CertUtil
- Encrypting Files with WinRar or 7z
- Endpoint Security
- Enumeration Command Spawned via WMIPrvSE
- Enumeration of Administrator Accounts
- Enumeration of Kernel Modules
- Enumeration of Users or Groups via Built-in Commands
- Executable File Creation with Multiple Extensions
- Execution from Unusual Directory - Command Line
- Execution of COM object via Xwizard
- Execution of File Written or Modified by Microsoft Office
- Execution of File Written or Modified by PDF Reader
- Execution of Persistent Suspicious Program
- Execution via Electron Child Process Node.js Module
- Execution via MSSQL xp_cmdshell Stored Procedure
- Execution via Regsvcs/Regasm
- Execution via TSClient Mountpoint
- Execution via local SxS Shared Module
- Execution with Explicit Credentials via Scripting
- Exploit - Detected - Elastic Endgame
- Exploit - Prevented - Elastic Endgame
- Exporting Exchange Mailbox via PowerShell
- External Alerts
- FTP (File Transfer Protocol) Activity to the Internet
- File Deletion via Shred
- File Permission Modification in Writable Directory
- File and Directory Discovery
- Finder Sync Plugin Registered and Enabled
- GCP Firewall Rule Creation
- GCP Firewall Rule Deletion
- GCP Firewall Rule Modification
- GCP IAM Custom Role Creation
- GCP IAM Role Deletion
- GCP IAM Service Account Key Deletion
- GCP Logging Bucket Deletion
- GCP Logging Sink Deletion
- GCP Logging Sink Modification
- GCP Pub/Sub Subscription Creation
- GCP Pub/Sub Subscription Deletion
- GCP Pub/Sub Topic Creation
- GCP Pub/Sub Topic Deletion
- GCP Service Account Creation
- GCP Service Account Deletion
- GCP Service Account Disabled
- GCP Service Account Key Creation
- GCP Storage Bucket Configuration Modification
- GCP Storage Bucket Deletion
- GCP Storage Bucket Permissions Modification
- GCP Virtual Private Cloud Network Deletion
- GCP Virtual Private Cloud Route Creation
- GCP Virtual Private Cloud Route Deletion
- Google Workspace API Access Granted via Domain-Wide Delegation of Authority
- Google Workspace Admin Role Deletion
- Google Workspace MFA Enforcement Disabled
- Google Workspace Role Modified
- Malware - Detected - Elastic Endgame
- Malware - Prevented - Elastic Endgame
- Microsoft 365 Exchange Anti-Phish Policy Deletion
- Microsoft 365 Exchange Anti-Phish Rule Modification
- Microsoft 365 Exchange DKIM Signing Configuration Disabled
- Microsoft 365 Exchange DLP Policy Removed
- Microsoft 365 Exchange Malware Filter Policy Deletion
- Microsoft 365 Exchange Malware Filter Rule Modification
- Microsoft 365 Exchange Management Group Role Assignment
- Microsoft 365 Exchange Safe Attachment Rule Disabled
- Microsoft 365 Exchange Safe Link Policy Disabled
- Microsoft 365 Exchange Transport Rule Creation
- Microsoft 365 Exchange Transport Rule Modification
- Microsoft 365 Teams Custom Application Interaction Allowed
- Microsoft 365 Teams External Access Enabled
- Microsoft 365 Teams Guest Access Enabled
- Microsoft Build Engine Loading Windows Credential Libraries
- Microsoft Build Engine Started an Unusual Process
- Microsoft Build Engine Started by a Script Process
- Microsoft Build Engine Started by a System Process
- Microsoft Build Engine Started by an Office Application
- Microsoft Build Engine Using an Alternate Name
- Microsoft Exchange Server UM Spawning Suspicious Processes
- Microsoft Exchange Server UM Writing Suspicious Files
- Microsoft Exchange Worker Spawning Suspicious Processes
- Microsoft IIS Connection Strings Decryption
- Microsoft IIS Service Account Password Dumped
- Mimikatz Memssp Log File Detected
- Mknod Process Activity
- Modification of Boot Configuration
- Modification of Dynamic Linker Preload Shared Object
- Modification of Environment Variable via Launchctl
- Modification of OpenSSH Binaries
- Modification of Safari Settings via Defaults Command
- Modification of Standard Authentication Module or Configuration
- Modification of WDigest Security Provider
- Modification or Removal of an Okta Application Sign-On Policy
- Mounting Hidden or WebDav Remote Shares
- MsBuild Making Network Connections
- Mshta Making Network Connections
- Multi-Factor Authentication Disabled for an Azure User
- NTDS or SAM Database File Copied
- Net command via SYSTEM account
- Netcat Network Activity
- Network Connection via Certutil
- Network Connection via Compiled HTML File
- Network Connection via MsXsl
- Network Connection via Registration Utility
- Network Connection via Signed Binary
- Network Sniffing via Tcpdump
- New ActiveSyncAllowedDeviceID Added via PowerShell
- Nmap Process Activity
- Nping Process Activity
- Okta Brute Force or Password Spraying Attack
- Outbound Scheduled Task Activity via PowerShell
- PPTP (Point to Point Tunneling Protocol) Activity
- Peripheral Device Discovery
- Permission Theft - Detected - Elastic Endgame
- Permission Theft - Prevented - Elastic Endgame
- Persistence via DirectoryService Plugin Modification
- Persistence via Docker Shortcut Modification
- Persistence via Folder Action Script
- Persistence via Hidden Run Key Detected
- Persistence via KDE AutoStart Script or Desktop File Modification
- Persistence via Kernel Module Modification
- Persistence via Login or Logout Hook
- Persistence via Microsoft Office AddIns
- Persistence via Microsoft Outlook VBA
- Persistence via TelemetryController Scheduled Task Hijack
- Persistence via Update Orchestrator Service Hijack
- Persistence via WMI Event Subscription
- Persistent Scripts in the Startup Directory
- Port Forwarding Rule Addition
- Possible Consent Grant Attack via Azure-Registered Application
- Possible FIN7 DGA Command and Control Behavior
- Possible Okta DoS Attack
- Potential Admin Group Account Addition
- Potential Application Shimming via Sdbinst
- Potential Command and Control via Internet Explorer
- Potential Cookies Theft via Browser Debugging
- Potential Credential Access via Windows Utilities
- Potential DLL SideLoading via Trusted Microsoft Programs
- Potential DNS Tunneling via Iodine
- Potential DNS Tunneling via NsLookup
- Potential Disabling of SELinux
- Potential Evasion via Filter Manager
- Potential Hidden Local User Account Creation
- Potential Kerberos Attack via Bifrost
- Potential LSA Authentication Package Abuse
- Potential Microsoft Office Sandbox Evasion
- Potential Modification of Accessibility Binaries
- Potential OpenSSH Backdoor Logging Activity
- Potential Password Spraying of Microsoft 365 User Accounts
- Potential Persistence via Atom Init Script Modification
- Potential Persistence via Cron Job
- Potential Persistence via Login Hook
- Potential Persistence via Periodic Tasks
- Potential Persistence via Time Provider Modification
- Potential Port Monitor or Print Processor Registration Abuse
- Potential Privacy Control Bypass via Localhost Secure Copy
- Potential Privacy Control Bypass via TCCDB Modification
- Potential Privilege Escalation via Sudoers File Modification
- Potential Process Herpaderping Attempt
- Potential Remote Desktop Tunneling Detected
- Potential Reverse Shell Activity via Terminal
- Potential SSH Brute Force Detected
- Potential Secure File Deletion via SDelete Utility
- Potential SharpRDP Behavior
- Potential Shell via Web Server
- Potential Windows Error Manager Masquerading
- PowerShell spawning Cmd
- Privilege Escalation via Named Pipe Impersonation
- Privilege Escalation via Root Crontab File Modification
- Privilege Escalation via Windir Environment Variable
- Process Activity via Compiled HTML File
- Process Discovery via Tasklist
- Process Execution from an Unusual Directory
- Process Injection - Detected - Elastic Endgame
- Process Injection - Prevented - Elastic Endgame
- Process Injection by the Microsoft Build Engine
- Process Termination followed by Deletion
- Program Files Directory Masquerading
- Prompt for Credentials with OSASCRIPT
- Proxy Port Activity to the Internet
- PsExec Network Connection
- Public IP Reconnaissance Activity
- Query Registry via reg.exe
- RDP (Remote Desktop Protocol) from the Internet
- RDP (Remote Desktop Protocol) to the Internet
- RDP Enabled via Registry
- RPC (Remote Procedure Call) from the Internet
- RPC (Remote Procedure Call) to the Internet
- Ransomware - Detected - Elastic Endgame
- Ransomware - Prevented - Elastic Endgame
- Rare AWS Error Code
- Registry Persistence via AppCert DLL
- Registry Persistence via AppInit DLL
- Remote Desktop Enabled in Windows Firewall
- Remote Execution via File Shares
- Remote File Copy to a Hidden Share
- Remote File Copy via TeamViewer
- Remote File Download via Desktopimgdownldr Utility
- Remote File Download via MpCmdRun
- Remote File Download via PowerShell
- Remote File Download via Script Interpreter
- Remote SSH Login Enabled via systemsetup Command
- Remote Scheduled Task Creation
- Remote System Discovery Commands
- Remotely Started Services via RPC
- Renamed AutoIt Scripts Interpreter
- Roshal Archive (RAR) or PowerShell File Downloaded from the Internet
- SIP Provider Modification
- SMB (Windows File Sharing) Activity to the Internet
- SMTP on Port 26/TCP
- SMTP to the Internet
- SQL Traffic to the Internet
- SSH (Secure Shell) from the Internet
- SSH (Secure Shell) to the Internet
- SSH Authorized Keys File Modification
- SUNBURST Command and Control Activity
- Scheduled Task Created by a Windows Script
- Scheduled Tasks AT Command Enabled
- Searching for Saved Credentials via VaultCmd
- Security Software Discovery using WMIC
- Security Software Discovery via Grep
- Sensitive Files Compression
- Service Command Lateral Movement
- Setuid / Setgid Bit Set via chmod
- Shell Execution via Apple Scripting
- Shortcut File Written or Modified for Persistence
- Socat Process Activity
- SoftwareUpdate Preferences Modification
- SolarWinds Process Disabling Services via Registry
- Spike in AWS Error Messages
- Startup Folder Persistence via Unsigned Process
- Startup or Run Key Registry Modification
- Strace Process Activity
- Sublime Plugin or Application Script Modification
- Sudo Heap-Based Buffer Overflow Attempt
- Sudoers File Modification
- Suspicious .NET Code Compilation
- Suspicious Activity Reported by Okta User
- Suspicious Automator Workflows Execution
- Suspicious Browser Child Process
- Suspicious Calendar File Modification
- Suspicious Child Process of Adobe Acrobat Reader Update Service
- Suspicious Cmd Execution via WMI
- Suspicious DLL Loaded for Persistence or Privilege Escalation
- Suspicious Emond Child Process
- Suspicious Endpoint Security Parent Process
- Suspicious Execution - Short Program Name
- Suspicious Execution via Scheduled Task
- Suspicious Explorer Child Process
- Suspicious Hidden Child Process of Launchd
- Suspicious Image Load (taskschd.dll) from MS Office
- Suspicious ImagePath Service Creation
- Suspicious JAR Child Process
- Suspicious MS Office Child Process
- Suspicious MS Outlook Child Process
- Suspicious Managed Code Hosting Process
- Suspicious PDF Reader Child Process
- Suspicious PowerShell Engine ImageLoad
- Suspicious Powershell Script
- Suspicious Print Spooler Point and Print DLL
- Suspicious PrintSpooler SPL File Created
- Suspicious PrintSpooler Service Executable File Creation
- Suspicious Process Execution via Renamed PsExec Executable
- Suspicious Process from Conhost
- Suspicious RDP ActiveX Client Loaded
- Suspicious SolarWinds Child Process
- Suspicious WMI Image Load from MS Office
- Suspicious WMIC XSL Script Execution
- Suspicious WerFault Child Process
- Suspicious Zoom Child Process
- Suspicious macOS MS Office Child Process
- Svchost spawning Cmd
- System Log File Deletion
- System Shells via Services
- SystemKey Access via Command Line
- TCC Bypass via Mounted APFS Snapshot Access
- TCP Port 8000 Activity to the Internet
- Tampering of Bash Command-Line History
- Telnet Port Activity
- Threat Detected by Okta ThreatInsight
- Timestomping using Touch Command
- Tor Activity to the Internet
- Trusted Developer Application Usage
- UAC Bypass Attempt via Elevated COM Internet Explorer Add-On Installer
- UAC Bypass Attempt via Privileged IFileOperation COM Interface
- UAC Bypass Attempt via Windows Directory Masquerading
- UAC Bypass Attempt with IEditionUpgradeManager Elevated COM Interface
- UAC Bypass via DiskCleanup Scheduled Task Hijack
- UAC Bypass via ICMLuaUtil Elevated COM Interface
- UAC Bypass via Windows Firewall Snap-In Hijack
- Uncommon Registry Persistence Change
- Unusual AWS Command for a User
- Unusual Child Process from a System Virtual Process
- Unusual Child Process of dns.exe
- Unusual Child Processes of RunDLL32
- Unusual City For an AWS Command
- Unusual Country For an AWS Command
- Unusual DNS Activity
- Unusual Executable File Creation by a System Critical Process
- Unusual File Creation - Alternate Data Stream
- Unusual File Modification by dns.exe
- Unusual Linux Network Activity
- Unusual Linux Network Connection Discovery
- Unusual Linux Network Port Activity
- Unusual Linux Network Service
- Unusual Linux Process Calling the Metadata Service
- Unusual Linux Process Discovery Activity
- Unusual Linux System Information Discovery Activity
- Unusual Linux System Network Configuration Discovery
- Unusual Linux System Owner or User Discovery Activity
- Unusual Linux User Calling the Metadata Service
- Unusual Linux Username
- Unusual Linux Web Activity
- Unusual Login Activity
- Unusual Network Activity from a Windows System Binary
- Unusual Network Connection via RunDLL32
- Unusual Network Destination Domain Name
- Unusual Parent Process for cmd.exe
- Unusual Parent-Child Relationship
- Unusual Persistence via Services Registry
- Unusual Process Execution - Temp
- Unusual Process Execution Path - Alternate Data Stream
- Unusual Process For a Linux Host
- Unusual Process For a Windows Host
- Unusual Process Network Connection
- Unusual Service Host Child Process - Childless Service
- Unusual Sudo Activity
- Unusual Web Request
- Unusual Web User Agent
- Unusual Windows Network Activity
- Unusual Windows Path Activity
- Unusual Windows Process Calling the Metadata Service
- Unusual Windows Remote User
- Unusual Windows Service
- Unusual Windows User Calling the Metadata Service
- Unusual Windows User Privilege Elevation Activity
- Unusual Windows Username
- User Account Creation
- User Added as Owner for Azure Application
- User Added as Owner for Azure Service Principal
- User Added to Privileged Group in Active Directory
- User Discovery via Whoami
- VNC (Virtual Network Computing) from the Internet
- VNC (Virtual Network Computing) to the Internet
- Virtual Machine Fingerprinting
- Virtual Private Network Connection Attempt
- Volume Shadow Copy Deletion via VssAdmin
- Volume Shadow Copy Deletion via WMIC
- WMI Incoming Lateral Movement
- Web Application Suspicious Activity: No User Agent
- Web Application Suspicious Activity: POST Request Declined
- Web Application Suspicious Activity: Unauthorized Method
- Web Application Suspicious Activity: sqlmap User Agent
- WebProxy Settings Modification
- WebServer Access Logs Deleted
- Whoami Process Activity
- Windows CryptoAPI Spoofing Vulnerability (CVE-2020-0601 - CurveBall)
- Windows Defender Disabled via Registry Modification
- Windows Event Logs Cleared
- Windows Network Enumeration
- Windows Script Executing PowerShell
- Windows Script Interpreter Executing Process via WMI
- Windows Suspicious Script Object Execution
- Zoom Meeting with no Passcode
- macOS Installer Spawns Network Event
- Investigate events
- Cases
- Elastic Security APIs
- Detections API
- Exceptions API
- Lists API
- Detection Alerts Migration API
- Timeline API
- Cases API
- Create case
- Add comment
- Update case
- Update comment
- Find cases
- Get case
- Get all case comments
- Get comment
- Get all case activity
- Get tags
- Get reporters
- Get status
- Delete comment
- Delete all comments
- Delete case
- Set default Elastic Security UI connector
- Update case configurations
- Get current connector
- Find connectors
- Push case
- Add external details to case
- Actions API (for pushing cases to external systems)
- Elastic Security fields and object schemas
- Enable process analyzer after an upgrade
- Release Notes
Monitor and troubleshoot rule executions
editMonitor and troubleshoot rule executions
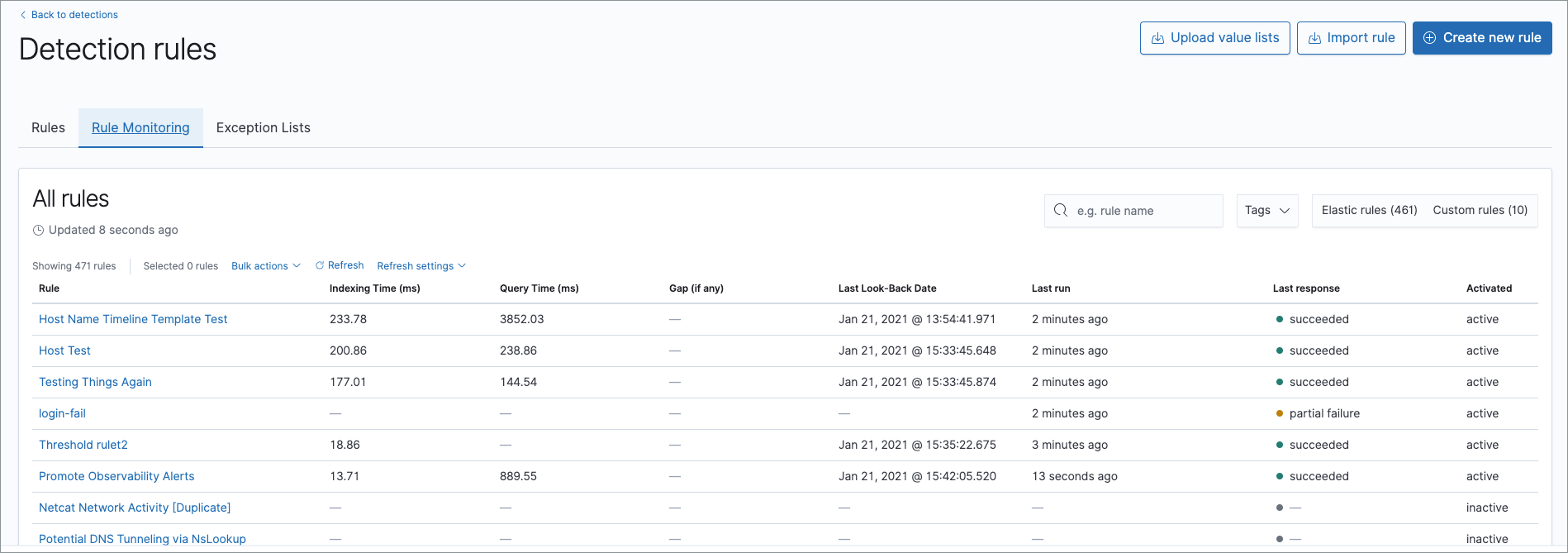
editTo view a summary of all rule executions, such as failures and last execution times, select the Rule Monitoring tab in the All rules table (Security → Detections → Manage detection rules).
For detailed information on a rule, its generated alerts and errors, click on a rule name in the All rules table.
Troubleshoot missing alerts
editWhen a rule fails to run close to its scheduled time, some alerts may be missing. There are a number of steps you can perform to try and resolve this issue.
If you see Gaps in the All rules table or on the Rule details page
for a small number of rules, you can increase those rules'
Additional look-back time (Detection rules page → the rule’s All actions button (…) → Edit rule settings → Schedule → Additional look-back time).
If the rule that experiences gaps is an indicator match rule, see how to tune indicator match rules. Also please note that Elastic Security provides limited support for indicator match rules.
If you see gaps for numerous rules:
- If you restarted Kibana when many rules were activated, try deactivating them and then reactivating them in small batches at staggered intervals. This ensures Kibana does not attempt to run all the rules at the same time.
- Consider adding another Kibana instance to your environment.
Even if your rule runs at its scheduled time, there might still be missing alerts if your ingestion pipeline delay is greater than your rule interval + additional look-back time. Prebuilt rules have a minimum interval + additional look-back time of 6 minutes in Elastic Stack version >=7.11.0. To avoid missed alerts for prebuilt rules, use caution to ensure that ingestion pipeline delays remain below 6 minutes.
In addition, use caution when creating custom rule schedules to ensure that the specified interval + additional look-back time is greater than your deployment’s ingestion pipeline delay.
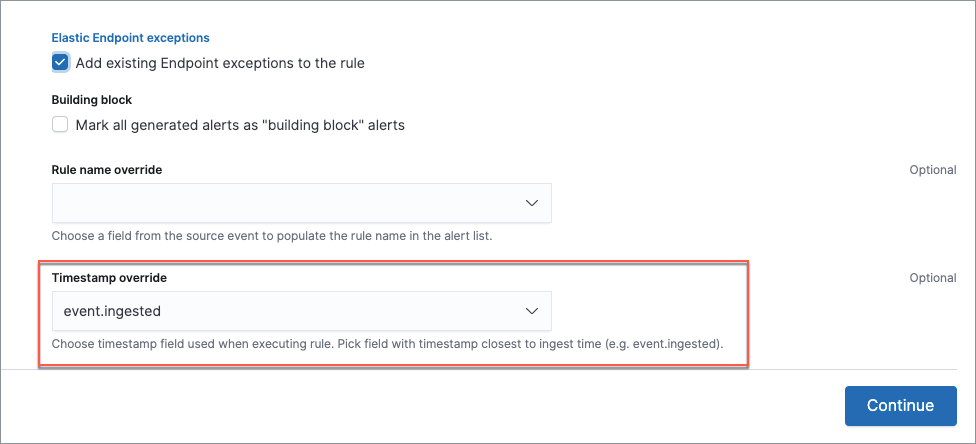
You can eliminate the risk of missed alerts due to ingestion pipeline delay by specifying the Timestamp override field value to event.ingested in advanced settings during rule creation or editing. The detection engine uses the value from the event.ingested field as the timestamp when executing the rule.
For example, if an event occurred at 10:01, and due to a 9-minute ingestion pipeline delay, was ingested into Elasticsearch at 10:10, a rule created to detect that event, with an interval + additional look-back time of 6 minutes, even if executing at 10:12 — 11 minutes after the event occurred — would still detect the event since the event.ingested timestamp was only two minutes earlier, well within the 6-minute rule query.
Troubleshoot missing alerts for machine learning jobs
editThe prebuilt machine learning jobs have dependencies on data fields that are populated by Beats and Elastic Agent integrations. In version 7.11, new machine learning jobs (Security: Linux and Security: Windows) were provided, which operate on newer ECS fields than the previous Security: Winlogbeat and Security: Auditbeat jobs. However, the prebuilt rules were not updated to use the new machine learning jobs.
Therefore:
- If you have only 7.10 or earlier versions of Beats, you can continue using the Security:Auditbeat and Security:Winlogbeat machine learning jobs and the prebuilt machine learning rules that have been in the Elastic Security app since version 7.5.
- If you have only 7.11 or later versions of Beats, use the Security:Linux and Security:Windows machine learning jobs. If you want to generate alerts for anomalies in these jobs, make clones of the existing machine learning rules and update them to use the new jobs.
- If you have a mix of old and new versions of Beats or you have a mix of Beats and Elastic Endpoint integrations, use both the old and new machine learning jobs. If you want alerts for anomalies in the new jobs, make clones of the existing machine learning rules and update them to use the new jobs.
- If you have a non-Elastic data shipper that gathers ECS-compatible Windows events, use the Security:Windows machine learning jobs. If you want alerts for anomalies in these jobs, make clones of the existing machine learning rules and update them to use these jobs.
If you are cloning prebuilt machine learning rules to generate alerts for the new machine learning jobs, the following rules are affected:
-
Unusual Linux Network Port Activity: Use
v2_linux_anomalous_network_port_activity_ecsinstead oflinux_anomalous_network_port_activity_ecs. -
Anomalous Process For a Linux Population: Use
v2_linux_anomalous_process_all_hosts_ecsinstead oflinux_anomalous_process_all_hosts_ecs. -
Unusual Linux Username: Use
v2_linux_anomalous_user_name_ecsinstead oflinux_anomalous_user_name_ecs. -
Unusual Linux Process Calling the Metadata Service: Use
v2_linux_rare_metadata_processinstead oflinux_rare_metadata_process. -
Unusual Linux User Calling the Metadata Service: Use
v2_linux_rare_metadata_userinstead oflinux_rare_metadata_user. -
Unusual Process For a Linux Host: Use
v2_rare_process_by_host_linux_ecsinstead ofrare_process_by_host_linux_ecs. -
Unusual Process For a Windows Host: Use
v2_rare_process_by_host_windows_ecsinstead ofrare_process_by_host_windows_ecs. -
Unusual Windows Network Activity: Use
v2_windows_anomalous_network_activity_ecsinstead ofwindows_anomalous_network_activity_ecs. -
Unusual Windows Path Activity: Use
v2_windows_anomalous_path_activity_ecsinstead ofwindows_anomalous_path_activity_ecs. -
Anomalous Windows Process Creation: Use
v2_windows_anomalous_process_creationinstead ofwindows_anomalous_process_creation. -
Anomalous Process For a Windows Population: Use
v2_windows_anomalous_process_all_hosts_ecsinstead ofwindows_anomalous_process_all_hosts_ecs. -
Unusual Windows Username: Use
v2_windows_anomalous_user_name_ecsinstead ofwindows_anomalous_user_name_ecs. -
Unusual Windows Process Calling the Metadata Service: Use
v2_windows_rare_metadata_processinstead ofwindows_rare_metadata_process. -
Unusual Windows User Calling the Metadata Service: Use
v2_windows_rare_metadata_userinstead ofwindows_rare_metadata_user.