One-way and mutual TLS certifications flow
editOne-way and mutual TLS certifications flow
editThis page provides an overview of the relationship between the various certificates and certificate authorities (CAs) that you configure for Fleet Server and Elastic Agent, using the elastic-agent install TLS command options.
Simple one-way TLS connection
editThe following elastic-agent install command configures a Fleet Server with the required certificates and certificate authorities to enable one-way TLS connections between the components involved:
elastic-agent install --url=https://your-fleet-server.elastic.co:443 \ --certificate-authorities=/path/to/fleet-ca \ --fleet-server-es=https://es.elastic.com:443 \ --fleet-server-es-ca=/path/to/es-ca \ --fleet-server-cert=/path/to/fleet-cert \ --fleet-server-cert-key=/path/to/fleet-cert-key \ --fleet-server-service-token=FLEET-SERVER-SERVICE-TOKEN \ --fleet-server-policy=FLEET-SERVER-POLICY-ID \ --fleet-server-port=8220
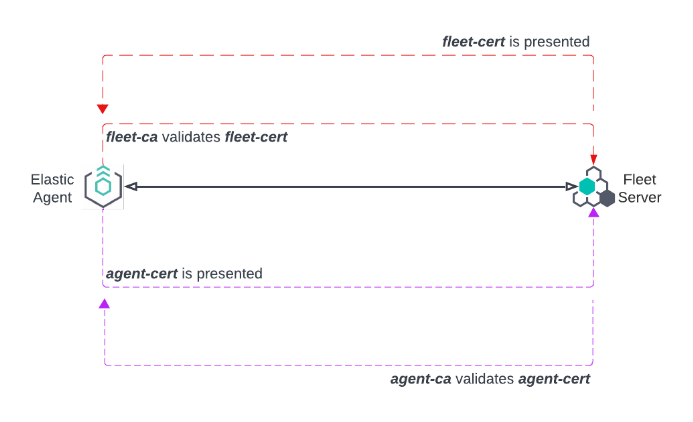
Elastic Agent is configured with fleet-ca as the certificate authority that it needs to validate certificates from Fleet Server.
During the TLS connection setup, Fleet Server presents its certificate fleet-cert to the agent and the agent (as a client) uses fleet-ca to validate the presented certificate.
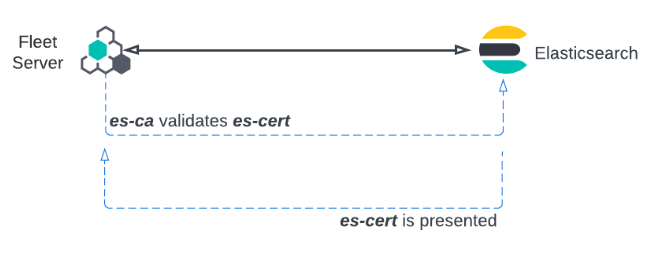
Fleet Server also establishes a secure connection to an Elasticsearch cluster. In this case, Fleet Server is configured with the certificate authority from the Elasticsearch es-ca. Elasticsearch presents its certificate, es-cert, and Fleet Server validates the presented certificate using the certificate authority es-ca.
Relationship between components in a one-way TLS connection
edit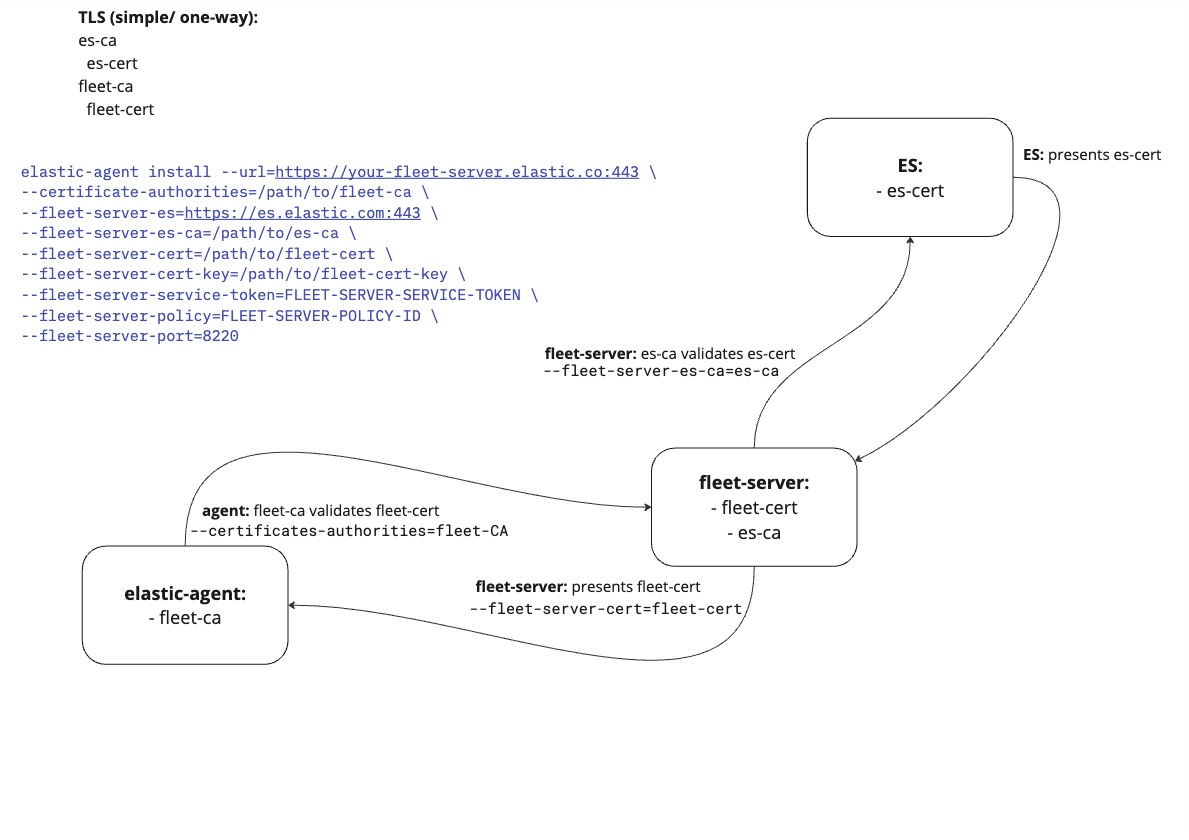
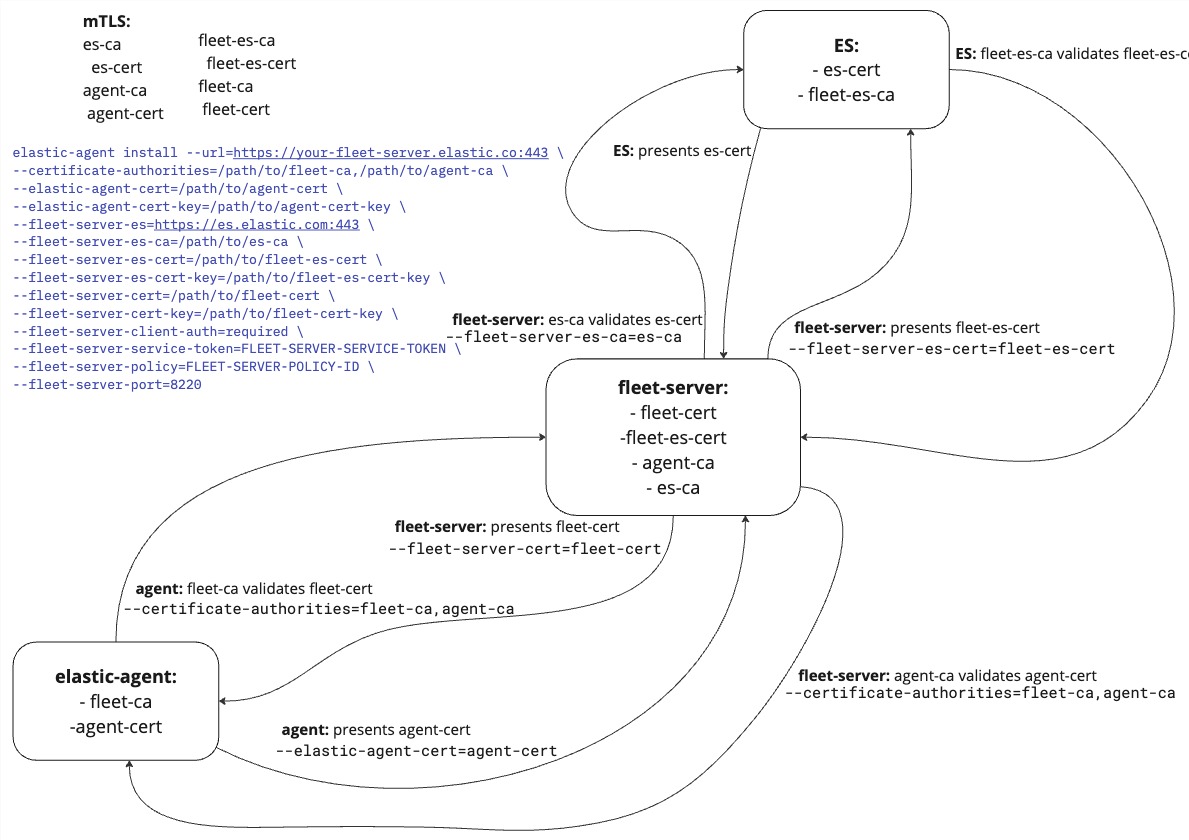
Mutual TLS connection
editThe following elastic-agent install command configures a Fleet Server with the required certificates and certificate authorities to enable mutual TLS connections between the components involved:
elastic-agent install --url=https://your-fleet-server.elastic.co:443 \ --certificate-authorities=/path/to/fleet-ca,/path/to/agent-ca \ --elastic-agent-cert=/path/to/agent-cert \ --elastic-agent-cert-key=/path/to/agent-cert-key \ --fleet-server-es=https://es.elastic.com:443 \ --fleet-server-es-ca=/path/to/es-ca \ --fleet-server-es-cert=/path/to/fleet-es-cert \ --fleet-server-es-cert-key=/path/to/fleet-es-cert-key \ --fleet-server-cert=/path/to/fleet-cert \ --fleet-server-cert-key=/path/to/fleet-cert-key \ --fleet-server-client-auth=required \ --fleet-server-service-token=FLEET-SERVER-SERVICE-TOKEN \ --fleet-server-policy=FLEET-SERVER-POLICY-ID \ --fleet-server-port=8220
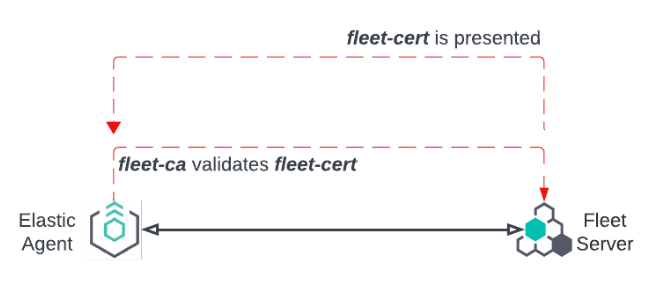
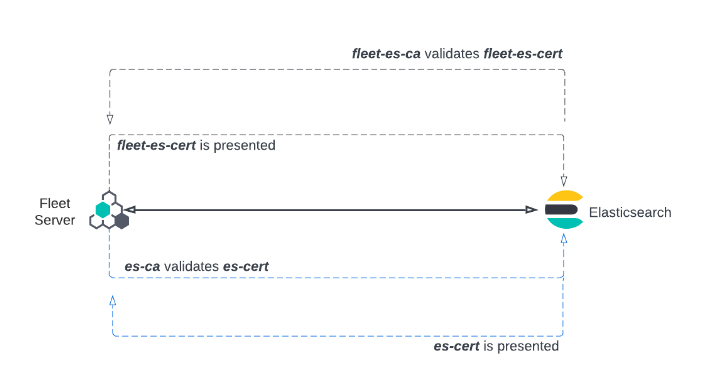
As with the one-way TLS example, Elastic Agent is configured with fleet-ca as the certificate authority that it needs to validate certificates from the Fleet Server. Fleet Server presents its certificate fleet-cert to the agent and the agent (as a client) uses fleet-ca to validate the presented certificate.
To establish a mutual TLS connection, the agent presents its certificate, agent-cert, and Fleet Server validates this certificate using the agent-ca that it has stored in memory.
Fleet Server can also establish a mutual TLS connection to the Elasticsearch cluster. In this case, Fleet Server is configured with the certificate authority from the Elasticsearch es-ca and uses this to validate the certificate es-cert presented to it by Elasticsearch.
Note that you can also configure mutual TLS for Fleet Server and Elastic Agent using a proxy.
Relationship between components in a mutual TLS connection
edit