The endpoint tax is over
Bury restrictive per-endpoint fees and deploy world-class protection with Elastic Security. Analyze critical context and stop attacks instantly with a single agentic security operations platform that includes top-rated XDR with your SIEM.

ANALYST REPORT
Elastic was named a Leader in the IDC MarketScape for Worldwide XDR Software 2025 Vendor Assessment.

INDUSTRY TEST
Elastic is the only vendor with 100% protection rates in all of AV‑Comparatives’ 2025 Business Security Tests.
You're in good company
See how companies like yours use Elastic Security.
Customer spotlight
By replacing multiple tools with Elastic Security, Texas A&M freed up 100+ analyst hours every month and reduced response times by 99%.
Customer spotlight

THG Ingenuity cut response times by 60% and halved first-line triage time with Elastic Security, while also reducing storage costs.
Customer spotlight

AHEAD cut triage time by 73% and automated 92% of resolutions with Elastic Security, holding MTTR under seven minutes for industry-leading response.
PROTECT & RESPOND
XDR and SIEM in one agentic security operations platform
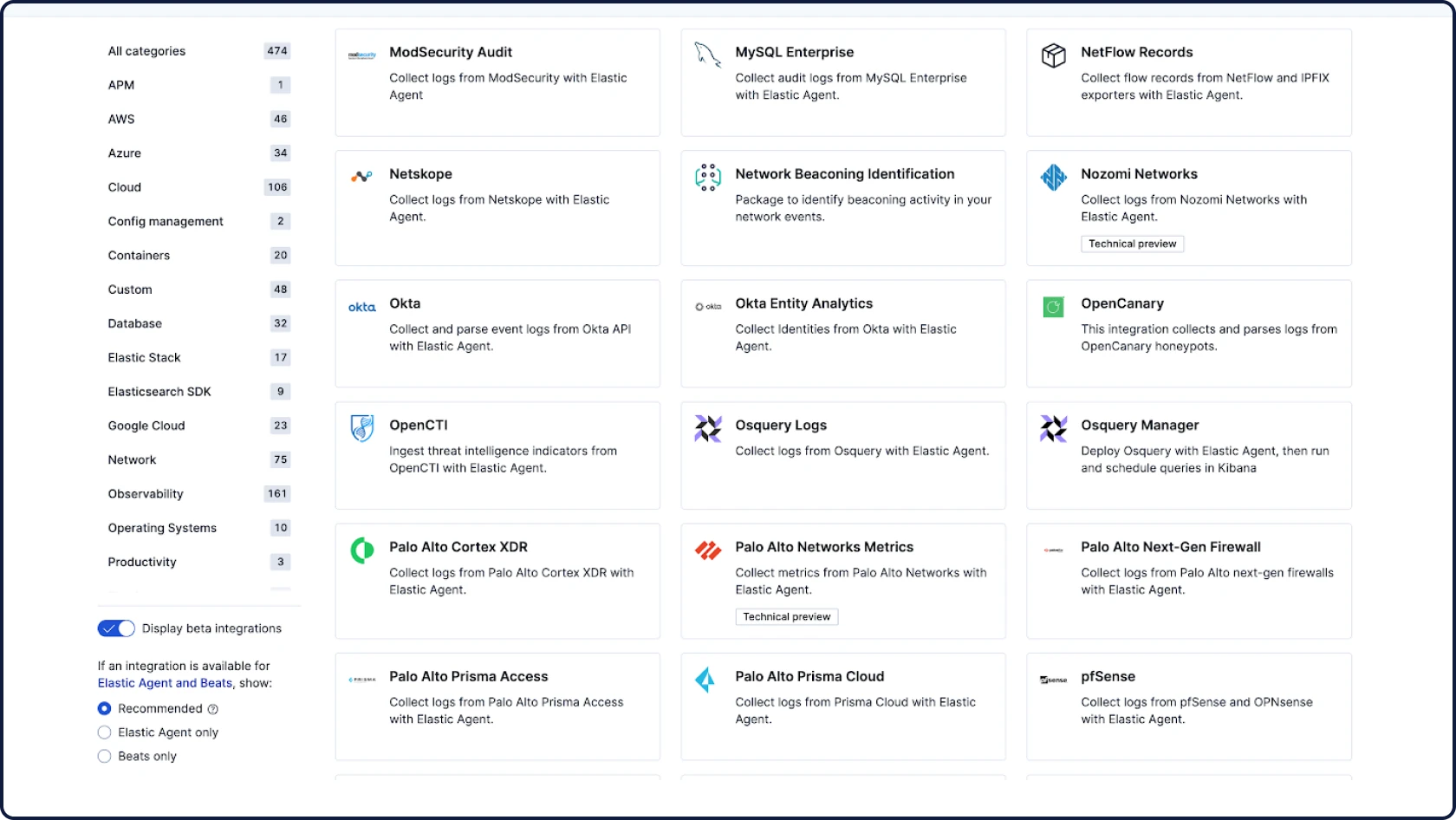
Analyze critical context and stop attacks instantly with a single platform that includes world-class XDR with your SIEM with zero per-endpoint fees.
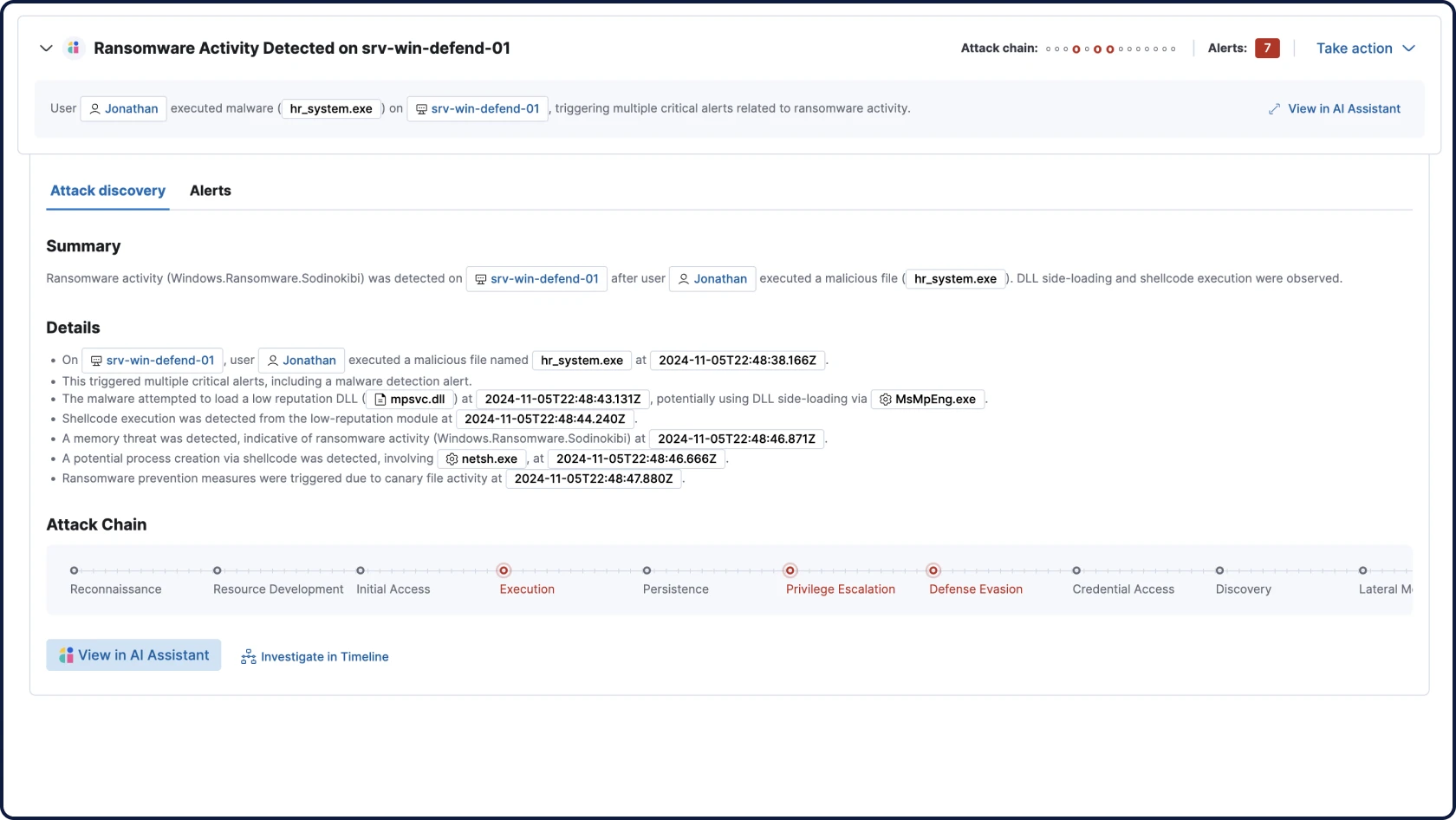
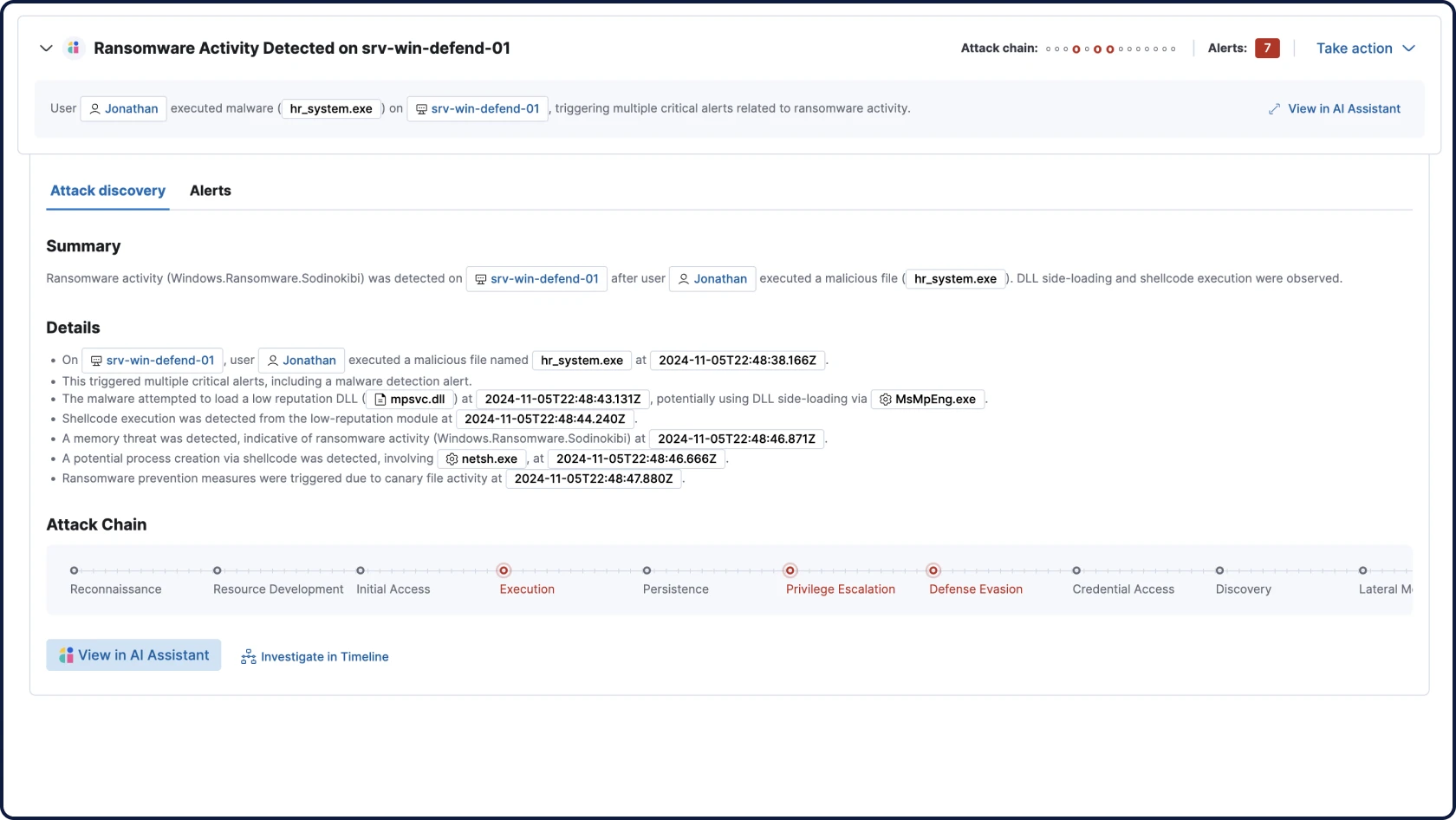
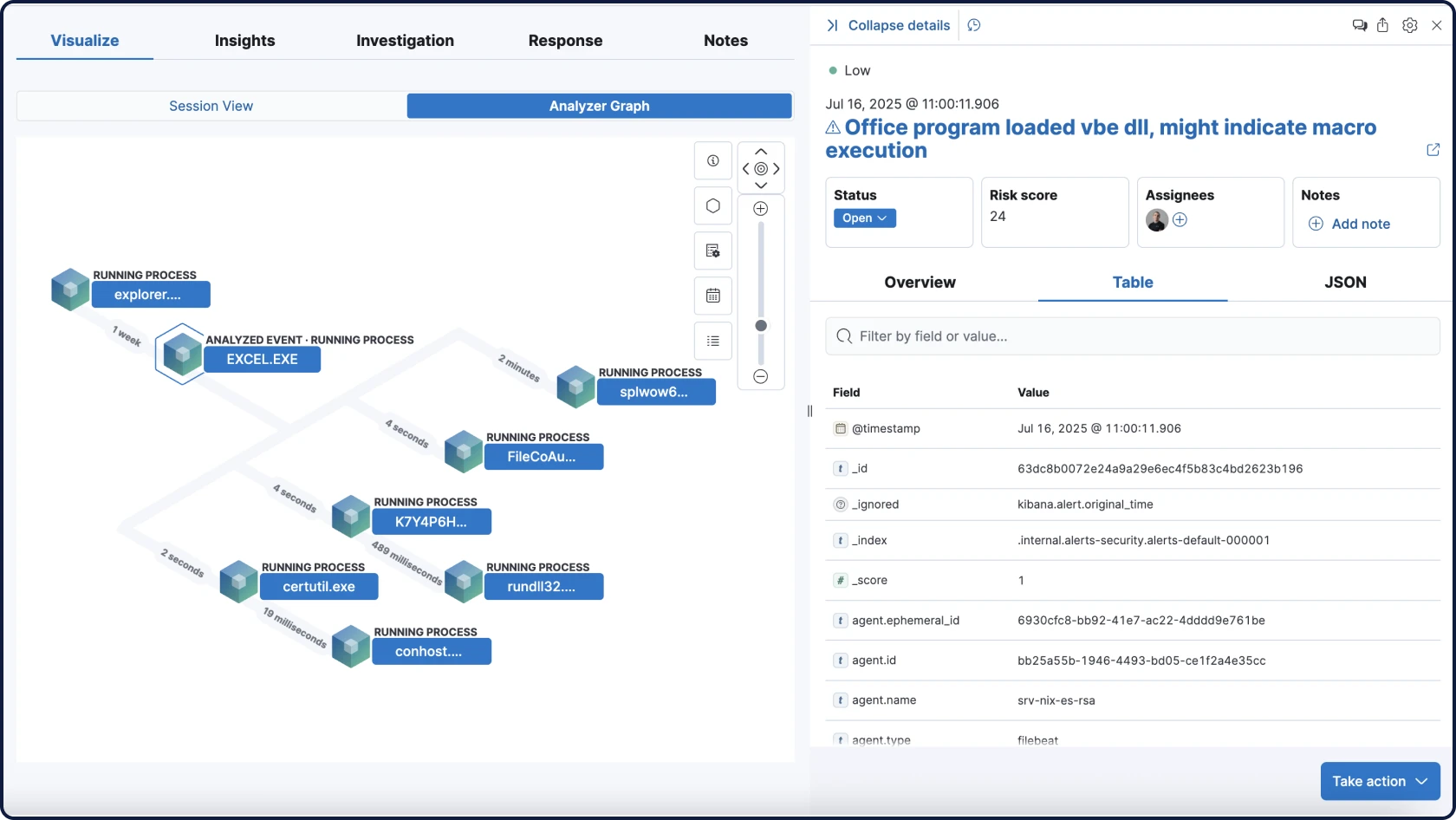
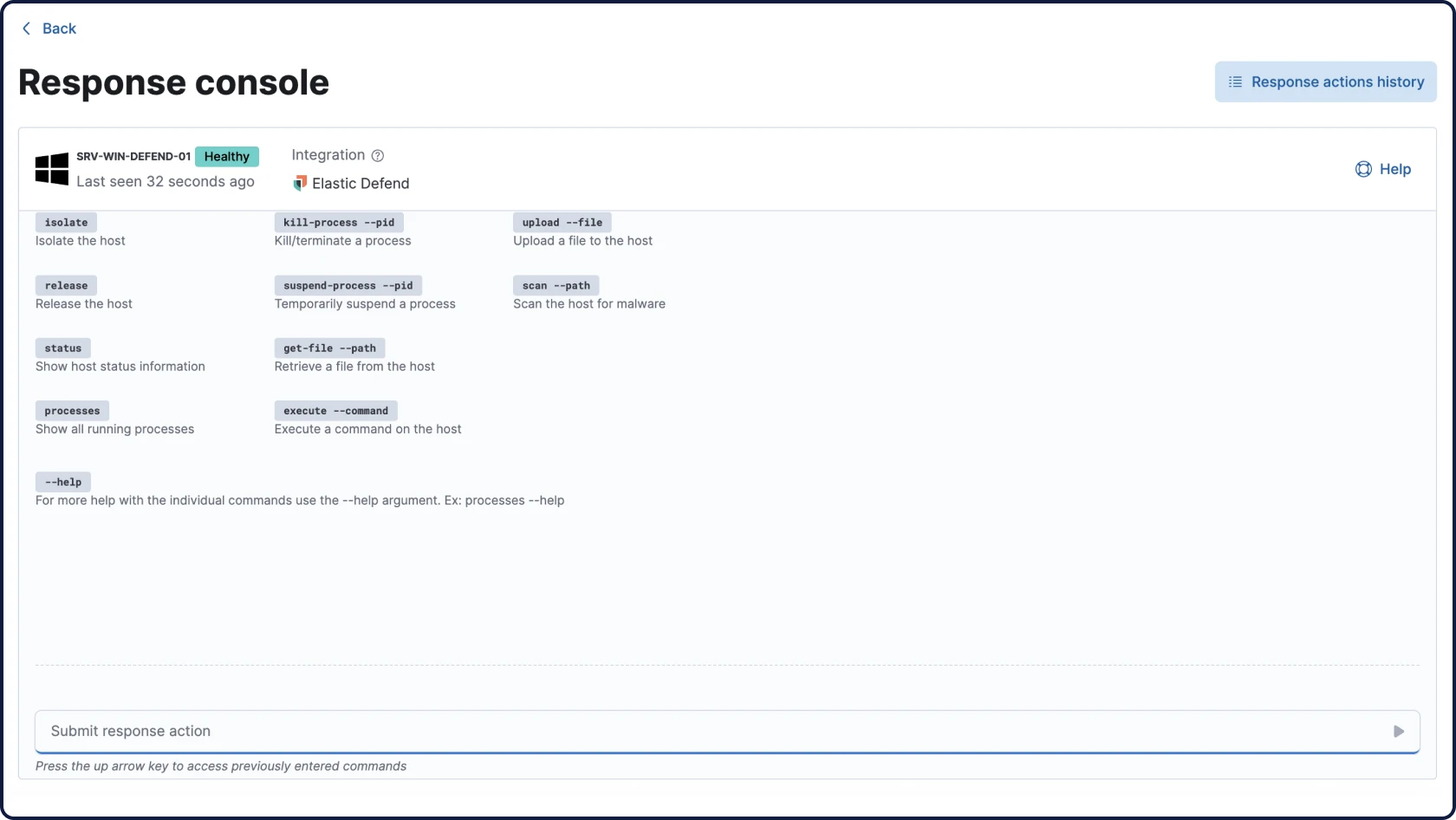
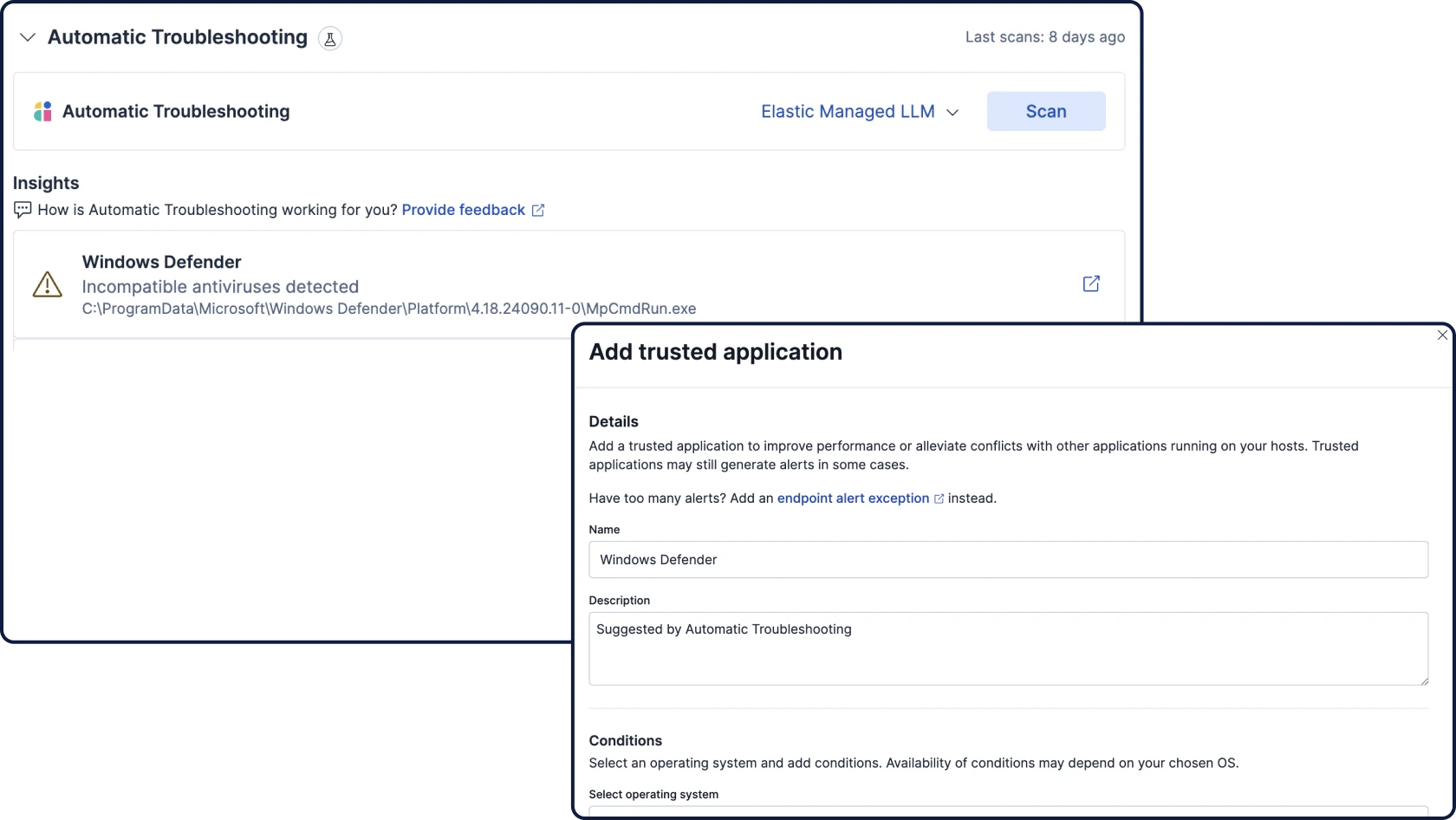
Attack Discovery mirrors the way analysts think, correlating alerts, behaviors, and attack paths across your extended security data with RAG-based context to automatically surface threats and guide triage and investigation.