Auditbeat quick start: installation and configuration
This guide describes how to get started quickly with audit data collection. You’ll learn how to:
- install Auditbeat on each system you want to monitor
- specify the location of your audit data
- parse log data into fields and send it to Elasticsearch
- visualize the log data in Kibana
You need Elasticsearch for storing and searching your data, and Kibana for visualizing and managing it.
To get started quickly, spin up an Elastic Cloud Hosted deployment. Elastic Cloud Hosted is available on AWS, GCP, and Azure. Try it out for free.
To install and run Elasticsearch and Kibana, see Installing the Elastic Stack.
Create an Elasticsearch Serverless project. Elasticsearch Serverless projects are available for Elasticsearch, Observability, and Security use cases.
Install Auditbeat on all the servers you want to monitor.
To download and install Auditbeat, use the commands that work with your system:
curl -L -O https://artifacts.elastic.co/downloads/beats/auditbeat/auditbeat-9.3.0-amd64.deb
sudo dpkg -i auditbeat-9.3.0-amd64.deb
curl -L -O https://artifacts.elastic.co/downloads/beats/auditbeat/auditbeat-9.3.0-x86_64.rpm
sudo rpm -vi auditbeat-9.3.0-x86_64.rpm
curl -L -O https://artifacts.elastic.co/downloads/beats/auditbeat/auditbeat-9.3.0-darwin-x86_64.tar.gz
tar xzvf auditbeat-9.3.0-darwin-x86_64.tar.gz
curl -L -O https://artifacts.elastic.co/downloads/beats/auditbeat/auditbeat-9.3.0-linux-x86_64.tar.gz
tar xzvf auditbeat-9.3.0-linux-x86_64.tar.gz
Download the Auditbeat Windows zip file.
Extract the contents of the zip file into
C:\Program Files.Rename the
auditbeat-[version]-windows-x86_64directory toAuditbeat.Open a PowerShell prompt as an Administrator (right-click the PowerShell icon and select Run As Administrator).
From the PowerShell prompt, run the following commands to install Auditbeat as a Windows service:
PS > cd 'C:\Program Files\Auditbeat'
PS C:\Program Files\Auditbeat> .\install-service-auditbeat.ps1
If script execution is disabled on your system, you need to set the execution policy for the current session to allow the script to run. For example: PowerShell.exe -ExecutionPolicy UnRestricted -File .\install-service-auditbeat.ps1.
The base folder has changed from C:\ProgramData\ to C:\Program Files\
because the latter has stricter permissions. The home path (base for
state and logs) is now C:\Program Files\Auditbeat-Data.
The install script (install-service-auditbeat.ps1) will check whether
C:\ProgramData\Auditbeat exits and move it to C:\Program Files\Auditbeat-Data.
For more details on the installation script refer to: install script.
The commands shown are for AMD platforms, but ARM packages are also available. Refer to the download page for the full list of available packages.
Connections to Elasticsearch and Kibana are required to set up Auditbeat.
Set the connection information in auditbeat.yml. To locate this configuration file, see Directory layout.
Specify the cloud.id of your Elastic Cloud Hosted deployment, and set cloud.auth to a user who is authorized to set up Auditbeat. For example:
cloud.id: "staging:dXMtZWFzdC0xLmF3cy5mb3VuZC5pbyRjZWM2ZjI2MWE3NGJmMjRjZTMzYmI4ODExYjg0Mjk0ZiRjNmMyY2E2ZDA0MjI0OWFmMGNjN2Q3YTllOTYyNTc0Mw=="
cloud.auth: "auditbeat_setup:YOUR_PASSWORD"
- This examples shows a hard-coded password, but you should store sensitive values in the secrets keystore.
Set the host and port where Auditbeat can find the Elasticsearch installation, and set the username and password of a user who is authorized to set up Auditbeat. For example:
output.elasticsearch: hosts: ["https://myEShost:9200"] username: "auditbeat_internal" password: "YOUR_PASSWORD" ssl: enabled: true ca_trusted_fingerprint: "b9a10bbe64ee9826abeda6546fc988c8bf798b41957c33d05db736716513dc9c"- This example shows a hard-coded password, but you should store sensitive values in the secrets keystore.
- This example shows a hard-coded fingerprint, but you should store sensitive values in the secrets keystore. The fingerprint is a HEX encoded SHA-256 of a CA certificate, when you start Elasticsearch for the first time, security features such as network encryption (TLS) for Elasticsearch are enabled by default. If you are using the self-signed certificate generated by Elasticsearch when it is started for the first time, you will need to add its fingerprint here. The fingerprint is printed on Elasticsearch start up logs, or you can refer to connect clients to Elasticsearch documentation for other options on retrieving it. If you are providing your own SSL certificate to Elasticsearch refer to Auditbeat documentation on how to setup SSL.
If you plan to use our pre-built Kibana dashboards, configure the Kibana endpoint. Skip this step if Kibana is running on the same host as Elasticsearch.
setup.kibana: host: "mykibanahost:5601" username: "my_kibana_user" <2> password: "YOUR_PASSWORD"- The hostname and port of the machine where Kibana is running, for example,
mykibanahost:5601. If you specify a path after the port number, include the scheme and port:http://mykibanahost:5601/path. - The
usernameandpasswordsettings for Kibana are optional. If you don’t specify credentials for Kibana, Auditbeat uses theusernameandpasswordspecified for the Elasticsearch output. - To use the pre-built Kibana dashboards, this user must be authorized to view dashboards or have the
kibana_adminbuilt-in role.
- The hostname and port of the machine where Kibana is running, for example,
Set the Elasticsearch endpoint and API key in your Beat configuration file. To find your project's endpoint and create an API key, refer to connection details. For example:
output.elasticsearch:
hosts: ["ELASTICSEARCH_ENDPOINT_URL"]
api_key: "YOUR_API_KEY"
- This example shows a hard-coded API key, but you should store sensitive values in the secrets keystore. Refer to Grant access using API keys for more on API key configuration.
Do not use cloud.id or cloud.auth for Elasticsearch Serverless projects. Those settings are for Elastic Cloud Hosted deployments only.
To learn more about required roles and privileges, see Grant users access to secured resources.
You can send data to other outputs, such as Logstash, but that requires additional configuration and setup.
Auditbeat uses modules to collect audit information.
By default, Auditbeat uses a configuration that’s tailored to the operating system where Auditbeat is running.
To use a different configuration, change the module settings in auditbeat.yml.
The following example shows the file_integrity module configured to generate events whenever a file in one of the specified paths changes on disk:
auditbeat.modules:
- module: file_integrity
paths:
- /bin
- /usr/bin
- /sbin
- /usr/sbin
- /etc
To test your configuration file, change to the directory where the Auditbeat binary is installed, and run Auditbeat in the foreground with the following options specified: ./auditbeat test config -e. Make sure your config files are in the path expected by Auditbeat (see Directory layout), or use the -c flag to specify the path to the config file.
For more information about configuring Auditbeat, also see:
- Configure Auditbeat
- Config file format
auditbeat.reference.yml: This reference configuration file shows all non-deprecated options. You’ll find it in the same location asauditbeat.yml.
Auditbeat comes with predefined assets for parsing, indexing, and visualizing your data. To load these assets:
Make sure the user specified in
auditbeat.ymlis authorized to set up Auditbeat.From the installation directory, run:
auditbeat setup -eauditbeat setup -e./auditbeat setup -e./auditbeat setup -ePS > .\auditbeat.exe setup -e-eis optional and sends output to standard error instead of the configured log output.
By default Windows log files are stored in C:\Program Files\Auditbeat-Data\logs.
In versions before 9.0.6, the default location for Windows log files was C:\ProgramData\auditbeat\logs.
This step loads the recommended index template for writing to Elasticsearch and deploys the sample dashboards for visualizing the data in Kibana.
A connection to Elasticsearch (or Elastic Cloud Hosted) is required to set up the initial environment. If you're using a different output, such as Logstash, see Load the Elasticsearch index template > Load the index template manually and Load Kibana dashboards.
Before starting Auditbeat, modify the user credentials in auditbeat.yml and specify a user who is authorized to publish events.
To start Auditbeat, run:
sudo service auditbeat start
If you use an init.d script to start Auditbeat, you can’t specify command line flags (see Command reference). To specify flags, start Auditbeat in the foreground.
Also see Auditbeat and systemd.
sudo service auditbeat start
If you use an init.d script to start Auditbeat, you can’t specify command line flags (see Command reference). To specify flags, start Auditbeat in the foreground.
Also see Auditbeat and systemd.
sudo chown root auditbeat.yml
sudo ./auditbeat -e
- You’ll be running Auditbeat as root, so you need to change ownership of the configuration file, or run Auditbeat with
--strict.perms=falsespecified. See Config File Ownership and Permissions.
sudo chown root auditbeat.yml
sudo ./auditbeat -e
- You’ll be running Auditbeat as root, so you need to change ownership of the configuration file, or run Auditbeat with
--strict.perms=falsespecified. See Config File Ownership and Permissions.
PS C:\Program Files\auditbeat> Start-Service auditbeat
By default Windows log files are stored in C:\Program Files\Auditbeat-Data\logs.
In versions before 9.0.6, the default location for Windows log files was C:\ProgramData\auditbeat\logs.
Auditbeat should begin streaming events to Elasticsearch.
If you see a warning about too many open files, you need to increase the ulimit. See the FAQ for more details.
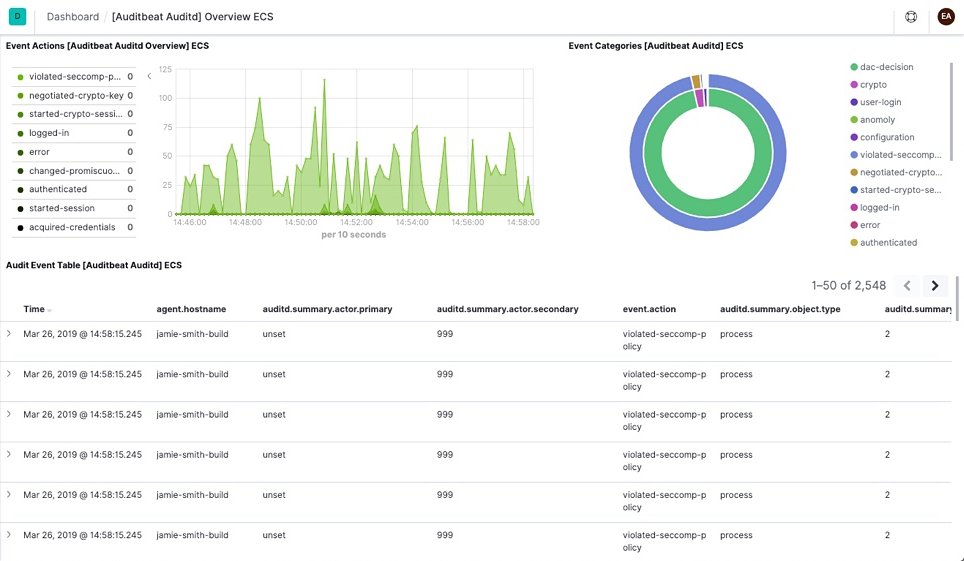
To make it easier for you to start auditing the activities of users and processes on your system, Auditbeat comes with pre-built Kibana dashboards and UIs for visualizing your data.
To open the dashboards:
Launch Kibana:
- Log in to your Elastic Cloud account.
- Navigate to the Kibana endpoint in your deployment.
Point your browser to http://localhost:5601, replacing
localhostwith the name of the Kibana host.Navigate to your Elasticsearch Serverless project in the Elastic Cloud console.
In the side navigation, click Discover. To see Auditbeat data, make sure the predefined
auditbeat-*data view is selected.TipIf you don’t see data in Kibana, try changing the time filter to a larger range. By default, Kibana shows the last 15 minutes.
In the side navigation, click Dashboard, then select the dashboard that you want to open.
The dashboards are provided as examples. We recommend that you customize them to meet your needs.
Now that you have audit data streaming into Elasticsearch, learn how to unify your logs, metrics, uptime, and application performance data.
Ingest data from other sources by installing and configuring other Elastic Beats:
Elastic Beats To capture Metricbeat Infrastructure metrics Filebeat Logs Winlogbeat Windows event logs Heartbeat Uptime information APM Application performance metrics Use the Observability apps in Kibana to search across all your data:
Elastic apps Use to Metrics app Explore metrics about systems and services across your ecosystem Logs app Tail related log data in real time Uptime app Monitor availability issues across your apps and services APM app Monitor application performance SIEM app Analyze security events